

Find the exact location of any phone. If I had to pick my favorite smartphone features, GPS would be near the top of the list.

It keeps me from getting lost in unfamiliar places, tracks the mileage of my morning jogs, helps me keep tabs on where my son is located and so much more. Of course, if my phone and apps know where I am, then that means a lot of other people could, too. App developers, advertisers, the government - anyone can tap into the information if I install the wrong app or don't pay attention to my settings.
OSINT. OSINT and other intel. Collection Software. Tools. Bank card number. Payment card numbers are found on payment cards, such as credit cards and debit cards, as well as stored-value cards, gift cards and other similar cards.
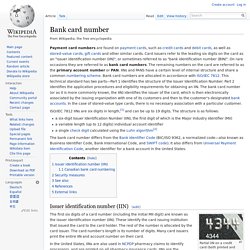
Card issuers refer to the leading six digits on the card as an "issuer identification number (IIN)", or sometimes referred to as "bank identification number (BIN)". On rare occasions they are referred to as bank card numbers. HHS.gov.
Data. Open Data Structures. WikiLeaks Finally Brings Back Its Submission System for Your Secrets. Updated at 6:30 pm with a statement from WikiLeaks founder Julian Assange.

It’s taken close to half a decade. But WikiLeaks is back in the business of accepting truly anonymous leaks. On Friday, the secret-spilling group announced that it has finally relaunched a beta version of its leak submission system, a file-upload site that runs on the anonymity software Tor to allow uploaders to share documents and tips while protecting their identity from any network eavesdropper, and even from WikiLeaks itself. The relaunch of that page—which in the past served as the core of WikiLeaks’ transparency mission—comes four and a half years after WikiLeaks’ last submission system went down amid infighting between WikiLeaks’ leaders and several of its disenchanted staffers.
Update: Spy agencies hacked SIM card maker's encryption. U.S. and U.K. intelligence agencies have reportedly hacked into the computer network of giant SIM card maker Gemalto and taken smartphone encryption keys potentially used by customers of hundreds of mobile phone carriers worldwide.

The Gemalto hack, by the U.S. National Security Agency and the U.K. Government Communications Headquarters (GCHQ), allowed the two spy agencies to monitor a large portion of the world's mobile phone voice and data traffic, according to a story in The Intercept. Guide to building the Tastic RFID Thief. The Tastic RFID Thief has been around since late 2013, and since I've had a tremendous amount of requests asking how to build it, I thought that this blog post would be of justice to the tastic.
About the Tastic RFID Thief The Tastic RFID Thief was introduced by the company Bishop Fox through a series of Defcon and Blackhat videos across mid-late 2013. Bishop Fox describe the Tastic silent, long-range RFID reader that can steal the proximity badge information from an unsuspecting employee as they physically walk near this concealed device. I built my first Tastic RFID Thief in February 2014, with no experience in electronics, and as a total challenge given to me by my boss at the time. It was an overall fun experience however, and I'm grateful that I was able to push myself. Cyber Threats against the Aviation Industry. Introduction The recent incident to the Malaysia Airlines Flight MH370 is fueling the discussion of whether would be possible to hack into an airplane and gain complete control control of on-board systems, excluding the pilots.

In the past, we have seen many security experts present possible attack scenarios, but never has an attacker made them reality. Zotero. Tool For Detecting social Netorks. Surveillance II. InfoSec. Knowledge worker. Intelligence Collection. Intelligence and Controversy in Democratic States. Central Intelligence Executive. Tools I use or am trying. OSINT. WiGLE - Wireless Geographic Logging Engine - Plotting WiFi on Maps. GFII - Guide Intelligence Economique. Midnight Research Labs - SEAT. SEAT aaron posted in on August 23rd, 2006 Project Info :: Features :: Screenshots :: Videos :: Downloads :: Documentation :: Developers :: WIKI Project info: SEAT (Search Engine Assessment Tool) is the next generation information digging application geared toward the needs of security professionals.
SEAT uses information stored in search engine databases, cache repositories, and other public resources to scan a site for potential vulnerabilities. File%20Shredding%20Programs.pdf. Encrypted Google. COMPUTER & TECHNO WORLD.
Ad. FBI. News Sources.