

Release-6. OpenSSH 6.9 has just been released.

It will be available from the mirrors listed at shortly. OpenSSH is a 100% complete SSH protocol version 1.3, 1.5 and 2.0 implementation and includes sftp client and server support. Once again, we would like to thank the OpenSSH community for their continued support of the project, especially those who contributed code or patches, reported bugs, tested snapshots or donated to the project.
More information on donations may be found at: Future Deprecation Notice ========================= The 7.0 release of OpenSSH, due for release in late July, will deprecate several features, some of which may affect compatibility or existing configurations. Charles Miller sur Twitter : "@coil780 @freebsdgirl This is why you should always buy tech books in German.
Arm/Raspberry Pi - FreeBSD Wiki. FreeBSD/ARM on Raspberry Pi FreeBSD-CURRENT has supported Raspberry Pi since November, 2012 and Raspberry Pi 2 since March, 2015.
If you have questions, ask on the freebsd-arm mailing list. What is Raspberry Pi? The Raspberry Pi launched in early 2012 as an inexpensive ($35) PC based on a Broadcom BCM2835 SoC. Build ngx_pagespeed From Source Fastly sur Twitter : "Thinking about migrating to a new CDN? Here are some questions you should be asking:... Nginx Secure SSL Web Server. Home RSS Search April 07, 2014 with HTTP, HTTPS SSL and Reverse Proxy Examples Nginx is a secure, fast and efficient web server. Network Tuning and Performance Guide. Home RSS Search November 12, 2013 Many of today's desktop systems and servers come with on board gigabit network controllers. Optimizing NGINX TLS Time To First Byte (TTTFB) By Ilya Grigorik on December 16, 2013 Network latency is one of our primary performance bottlenecks on the web.
In the worst case, new navigation requires a DNS lookup, TCP handshake, two roundtrips to negotiate the TLS tunnel, and finally a minimum of another roundtrip for the actual HTTP request and response — that's five network roundtrips to get the first few bytes of the HTML document! Modern browsers try very hard to anticipate and predict user activity to hide some of this latency, but speculative optimization is not a panacea: sometimes the browser doesn't have enough information, at other times it might guess wrong. This is why optimizing Time To First Byte (TTFB), and TLS TTFB in particular due to the extra roundtrips, is critical for delivering a consistent and optimized web experience.
The why and the how of TTFB. How to monitor ZFS with SNMP in FreeBSD? Moving away from puppet: SaltStack or Ansible? Over the past month at Lyft we’ve been working on porting our infrastructure code away from Puppet.
We had some difficulty coming to agreement on whether we wanted to use SaltStack (Salt) or Ansible. We were already using Salt for AWS orchestration, but we were divided on whether Salt or Ansible would be better for configuration management. BayLISA Monthly General Meeting - All Welcome - BayLISA (Sunnyvale, CA) DomainKeys Identified Mail. DomainKeys Identified Mail (DKIM) is an email validation system designed to detect email spoofing by providing a mechanism to allow receiving mail exchangers to check that incoming mail from a domain is authorized by that domain's administrators and that the email (including attachments) has not been modified during transport.
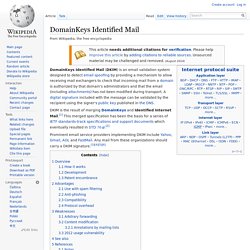
A digital signature included with the message can be validated by the recipient using the signer's public key published in the DNS. DKIM is the result of merging DomainKeys and Identified Internet Mail.[1] This merged specification has been the basis for a series of IETF standards-track specifications and support documents which eventually resulted in STD 76.[2] Continuous Delivery vs Continuous Deployment.
Translations: 한국말 Timothy Fitz’s blog entry on continuous deployment came out over a year before Dave and I published our book on continuous delivery.
So why did we choose a different name? Wesley David sur Twitter : "Whenever I see install instructions that start with curling a file into bash. #sysadmin #devops... Internet Protocol Version 6 Address Space. IPv6 address. Decomposition of an IPv6 address into its binary form IPv6 is the successor to the first addressing infrastructure of the Internet, Internet Protocol version 4 (IPv4).
In contrast to IPv4, which defined an IP address as a 32-bit value, IPv6 addresses have a size of 128 bits. Therefore, IPv6 has a vastly enlarged address space compared to IPv4. Remote execution tutorial. Before continuing make sure you have a working Salt installation by following the installation and the configuration instructions.
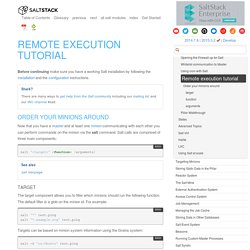
Now that you have a master and at least one minion communicating with each other you can perform commands on the minion via the salt command. Salt calls are comprised of three main components: salt '<target>' <function> [arguments] Command reference.