

Large Scale DDoS Attack on github.com. Neo Techno Ethica. Digiti$€ Bitcoin Technica. Are You Ready for Phone Numbers as Unique User Identity? Using the Web to support the social process has significantly increased in the last decade with the explosion of social network services like Facebook, LinkedIn, Twitter and online dating sites.

While having an online identity has certain strengths in providing easy communication by minimizing the need for a physical presence, the nature of online identities also has its flaws. It makes it easy for one to fake elements of one’s online identity, create a false identity or steal another person’s identity altogether. Creating a completely fake online identity The existence of a temporary virtual wall before one meets face-to- face also makes it easy to engage in fraud and spam online.
People can be duped into wiring large sums of money online to a “friend” or “lover” with whom they’ve only virtually communicated with. Most recently, a woman claimed to have wired $1.4 million to her online lover, whom she’d never met before. Stealing an online identity Phones as unique user identifier. U.S. Coding Website GitHub Hit With Cyberattack. BEIJING—A popular U.S. coding website is enduring an onslaught of Internet traffic meant for China’s most popular search engine, and security experts say the episode likely represents an attempt by China to shut down anticensorship tools.

The attack on San Francisco-based GitHub Inc., a service used by programmers and major tech firms world-wide to develop software, appears to underscore how China’s Internet censors increasingly reach outside the country to clamp down on content they find objectionable. The Cyberspace Administration of China didn’t respond to a request for comment Sunday. Security experts said the traffic onslaught—called a distributed denial-of-service attack in Internet circles—directed huge amounts of traffic from overseas users of Chinese search giant Baidu Inc. to GitHub, paralyzing GitHub’s website at times. Specifically, the traffic was directed to two GitHub pages that linked to copies of websites banned in China, the experts said. U.S. Coding Website GitHub Hit With Cyberattack.
Cyberspace Privacy. Cryptix. NeWeb Privacy. NeWeb Security. Web World Things. Internet tools. Internetworking. National Vulnerability Database Home. Your Clever Password Tricks Aren't Protecting You from Today's Hackers. CyberWar. Security - doxo. Doxo Provides Financial-Grade Security doxo utilizes security technologies and methods that meet or in many cases exceed those used by banks, brokerages, and other financial institutions.

Critical data and documents are always encrypted and stored securely. doxo systems are built by a team with deep experience developing secure, highly reliable transaction processing systems – systems that have processed billions of online and mobile transactions. doxo is designed to increase the security and privacy of your data. Mail, notes, files, bills and critical paper documents often contain sensitive and personal information. Unfortunately, paper documents often are stolen or become compromised. Doxo continuously monitors all accounts, takes action as needed to protect our systems and data, and notifies you if we identify security issues related to your account.
Connecting on doxo protects your security and privacy. You always decide when and if to connect with a provider. Krebs on Security. Endpoint Security Management Software FortiClient. Free removal of Viruses, Bots, Spyware, Keyloggers and Trojans. Will it run on my PC?

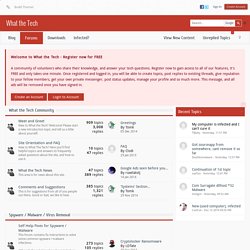
Unless you have a rather outdated PC from the late 90s, the answer is most likely yes, assuming that you’re using Windows XP, Vista, 7 or 8 - with the latest service pack installed. From Vista onwards all features are fully functional on x64 systems too. While running, Emsisoft Emergency Kit uses about 200 MB of your RAM which is quite low considering the 10 million signatures that it must load. If your PC has at least 1 GB of RAM, this will be perfect. Your Place for Tech Questions. Welcome to What the Tech - Register now for FREE A community of volunteers who share their knowledge, and answer your tech questions.
Register now to gain access to all of our features, it's FREE and only takes one minute. Advanced Cyberthreat Detection. Increased Security. GeoIP2 City. Return Path - The Global Leader in Email Intelligence. Marketing Exposed.