

Ivipid.com - StumbleUpon. Fromdev.com - StumbleUpon. Socialpositives.com - StumbleUpon. Www.supercompressor. Get up out of your seat and look at yourself in the mirror.
What do you see? An accomplished whiskey drinker who can tell the origins of a bottle by its color? Or an amateur who wouldn’t be able to differentiate the cheap stuff from a bottle of Yamakazi Sherry Cask Single Malt? Preferences aside, everyone can stand to get educated when it comes to the brown stuff. If you don’t know your Kentucky bourbon from Japanese whisky, allow yourself to be immersed in this article before you immerse yourself in booze. iStock What makes whiskey bourbon? This one’s a doozy, but bear with us. Bourbon tastes like: Its main characteristic is its sweetness, but it's also a bit smokey due to the charred oak. JackDaniels Is Tennessee Whiskey just bourbon with a different name? Glad you asked. Tennessee whiskey tastes like: Bourbon, if we're being honest.
Canadian Club What’s Canadian whisky? Canadian whisky (also spelled sans “e”) is actually interchangeable with the term “rye whisky” in Canada. What about rye? Topographic map Bargo River. Oneminutelist. Www.technonerdz. Whether you are a Penetration tester, a hacker or an aspiring newbie trying to learn Cyber Security, you must have a nice catalogue of tools to make your life easier.

While these tools do make working simpler but cannot compensate for the vast amount of knowledge required in this field. Ethical hacking and online security involves a lot efforts. Many tools are used to test and keep software secure. The same tools can also be used by hackers for exploitation. A hacking tool is a computer program or software which helps a hacker to hack a computer system or a computer program. In this post i’m going to mention 50 different tools under 9 categories that your ‘Hack Lab’ must have. Intrusion Detection Systems :- These are the tools you must have if you’re building a hack lab for penetration testing or for any security arrangement. SnortNetCop Encryption Tools :- While the above tools do identify any suspicious activity but they can’t protect your data, you need encryption tools for that. Ceriousproductions.
Changelog and Updates The following websites were part of the original list but they are either no longer available or have been replaced with better alternatives.

Www.instructables. (The above video was banned from YouTube on 9/12/2014 and hence has been re-uploaded to Vimeo.
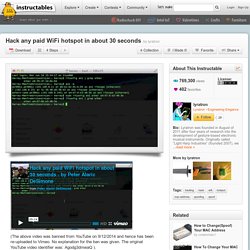
No explanation for the ban was given. The original YouTube video identifier was: Agodg3dmwaQ ). Or rather, DON'T hack any paid WiFi hotspots, as that would be bad... Also, don't turn your WiFi card off and then back on again after the hack to rectify any MAC address conflicts that might arise. The commands are: ifconfig en1 | grep ether arp -a sudo ifconfig en1 ether [mac address to spoof] Note that the term "MAC address" has nothing to do with Macintosh computers. Hacking-Tutorials. Learning to become hacker is not as easy as learning to become a software developer. I realized this when I started looking for learning resources for simple hacking people do. Even to start doing the simplest hack on own, a hacker requires to have in depth knowledge of multiple topics. Some people recommend minimum knowledge of few programming languages like C, Python, HTML with Unix operating system concepts and networking knowledge is required to start learning hacking techniques.
Where Should I Shop? - StumbleUpon. Download YouTube Videos. ✉ GuerrillaMail.com. Online converter - convert video, images, audio and documents for free. Convert Data, Files Online FREE: PDF, Word, Excel, Text, Images. 100 Websites You Should Know and Use. In the spring of 2007, Julius Wiedemann, editor in charge at Taschen GmbH, gave a legendary TED University talk: an ultra-fast-moving ride through the “100 websites you should know and use.”

Six years later, it remains one of the most viewed TED blog posts ever. Time for an update? We think so. Below, the 2013 edition of the 100 websites to put on your radar and in your browser. To see the original list, click here. And now, the original list from 2007, created by Julius Wiedemann, editor in charge at Taschen GmbH. Torrent Search Engine. Long Range Shooting Simulation Demo - StumbleUpon. Use your webcam to take photos online! Stealth - StumbleUpon.