

Back from the grave: ELF32 Universal Command Injector. Intercepting System Calls on x86_64 Windows. #sthash.ONE27G86. VHD_W7_Compact - Make Mini 7 - VHD_W7_Compact - Program to make Mini 7 Download and Run VHD_W7C.exe and Extract to simple path In Win 7/8 OS Set User Account Control Off and Reboot VHD_W7_Compact.exe - Make Portable W7 in 2 GB VHD booting from USB or HDDx64 version needs 3 GB VHD because of extra 1 GB SysWOW64 folder Source is Windows 7 x86 or x64 fresh installed in 10-15 GB VHD Or Install on primary active partition of internal harddisk.Target Boot Drive can be FAT32 or NTFS USB-drive used only for Boot files so that there are no changes for booting of internal harrddisk .Target System Drive must be NTFS and is the drive where the Win7 VHD file is created and this can be your internal harddisk drive.

Script. Updating Software with Group Policy - DeployHappiness. Updating software with Group Policy is the most difficult aspect of GPSI.

To make things complicated, the software you are upgrading may not have been deployed with Group Policy to begin with! So what is an administrator to do? How can we avoid blowing our legs off when we upgrade? Follow these steps and find out! Getting to ZTI - Importing Computers into the MDT Database with PowerShell - DeployHappiness. What is the MDT Database?

This guide will assume you already have MDT configured and that you have the MDT database setup (though not populated). If you aren’t at the step yet, you can keep reading but you might want to check out these two resources: When MDT is completely configured, you should have a full CustomSettings.ini that pre-populates most of your deployment settings. You will be left with a few options that have to be manually filled out though. The big two that have to be selected is the computer name and the Task Sequence. The MDT database links future deployments with existing computers. Blog: InstallShield Setup Silent Installation Switches. Those setup.exe files generated with InstallShield inherently support the creation and use of answer files that may be used to silent install applications.

Although it has no logic to handle anything not expected by the answerfile (more or less dialogs, more or less options in a dialog) it can be a helpful means of installation for some applications. The supported switches are as follows: Java For Complete Beginners - method calling. Methods don't do anything until you call them into action.

Before we see how, let's add another class to the project. We can then put all the methods there, instead of clogging up the main class. Les méthodes de classe. Java: Clear the console. TP sur les tableaux. Enable and Use Remote Commands in Windows PowerShell. The Windows PowerShell remoting features are supported by the WS-Management protocol and the Windows Remote Management (WinRM) service that implements WS-Management in Windows.
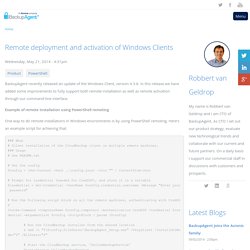
Computers running Windows 7 and later include WinRM 2.0 or later. On computers running earlier versions of Windows, you need to install WinRM 2.0 or later as appropriate and if supported. Currently, remoting is supported on Windows Vista with Service Pack 1 or later, Windows 7, Windows Server 2008, and Windows Server 2008 Release 2. You can verify the availability of WinRM and configure a PowerShell for remoting by following these steps: 1. Start Windows PowerShell as an administrator by right-clicking the Windows PowerShell shortcut and selecting Run As Administrator. 2. Problems With Installing Katana - Questions - Hak5 Forums. So here is my tale of the Katana install failures: I downloaded the .rar and extracted everything without a fuss.
Threw it onto a USB in the root (just like the site said, USB is formatted for fat32), then still following the site's install how-to, I find my way to the boot directory on the USB , and try to call . Missing NIC driver in WinPE boot image ? no problem - Niall C. Brady at myITforum.com. If you find yourself with some new hardware and are trying to PXE boot and you see WinPE downloading then restarting as soon as it loads, 9 times out of ten it's due to missing NIC (Network) drivers in your boot.wim image, this much we all know, but wouldnt it be nice to know exactly which driver we need to add to WinPE ?

Indeed it would as the process to add them usually takes quite some time. So how do you test which driver is actually the right one in WinPE, simply PXE boot the offending hardware and immediately bring up your Command prompt before it gets the chance to restart.. examing the SMSTS.log you'll probably see lines like Executing command line: "x:\sms\bin\i386\smstftp.exe" -i 192.168.3.2 get \SMSTemp\2011.08.31.13.51.53.0003.
Creating a Batch File to copy a directory [Solved] How to save a mail into an .eml-file with Outlook? Remote deployment and activation of Windows Clients. BackupAgent recently released an update of the Windows Client, version 4.3.8.
In this release we have added some improvements to fully support both remote installation as well as remote activation through our command-line interface. Example of remote installation using PowerShell remoting One way to do remote installations in Windows environments is by using PowerShell remoting. Direct Torrents - Download torrent files faster and safer as direct download. Windows Install ISOs. Windows Vista/7/8/10 Install ISOs require E2B to be on a 'Removable' USB drive.
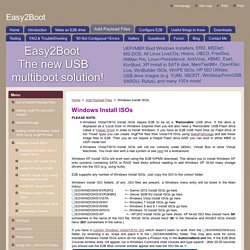
If the drive is displayed as a 'Local Disk' in Windows Explorer then you will also need a 'Removable' USB Flash drive called a 'Helper Drive' in order to install Windows. If you have an E2B USB Hard Disk (or Flash drive of the 'Fixed' type) you can create .imgPTN files from Vista/7/8 ISOs using MakePartImage and add these image files to E2B. Then you do not require a Helper Flash drive AND you can boot in either MBR or UEFI mode too! Windows Vista/7/8/10 Install ISOs will not run correctly under QEMU, Virtual Box or other Virtual Machines. You must test with a real system or see here for a workaround.
Project Chaos / CosMos (The Great Systems) This project started as tool development work for the IT Security group at Macquarie University in 2003 - a team that included Rob Dartnell, Ian Latter and Ty Miller. The need there was to demonstrate the weakness in one particular application's security, via its one hashed, network transmitted, password. The openMosix cluster software, at that time, was available via a number of Linux distributions, but these were neither secure nor dynamic enough to support the campus PC environment that the cluster software was to be deployed into. The CHAOS distribution was created to fill this need, and was developed for almost two years under the GPL to allow the openMosix community members to benefit from the security enhancements employed around the openMosix software (the clustering technology that is added to the Linux kernel). In mid to late 2004 CHAOS was adapted to the Cooperative Linux (coLinux) framework, allowing openMosix to run as a node on a Windows PC for the first time.
C.H.A.O.S. Linux. Java program to get input from user - Msc computer science. Compilation - Eclipse won't compile/run java file. Cracking Story – How I Cracked Over 122 Million SHA1 and MD5 Hashed Passwords « Thireus' Bl0g. This is the story about how I cracked 122 million* password hashes with John the Ripper and oclHashcat-plus. Author: m3g9tr0n, Copy Editor: Thireus. It was several months ago, when I (m3g9tr0n) saw a tweet from KoreLogic about a torrent file containing various password hash lists for a total of 146 million passwords. This very big amount of password hashes at first discouraged me, as I only own a classic computer configuration with an AMD Phenom II 4 cores at 3,2 Mhz in addition to an ATI/AMD 5770 graphics card.
But at least, I really wanted to give them a try because the field of password cracking fascinates me. The password cracking tools I used during this long trip were John the Ripper and oclHashcat-plus. [WinXP] How to write a LOGON program replace of logonui.exe. Typically the documentation will state what you can do, it doesn't states what you can't do. If it isn't explicitly documented that one can replace LogonUI it means you can't replace it. The logon desktop belongs to Winlogon any application other than GINA and credential providers can’t paint on that. This is a security feature in Windows. You also need to consider security obligation of your application. Your application accessing resources without any authenticated user logging in will be a security threat. You also need to consider, why is it important for a media player application run even if no one is logon. Tunneling your way out of corporate networks PART2: OpenVPN. The next way to tunnel out of corporate networks (that have an auth proxy, blahblablah,…) is using a SSL VPN.
Openvpn ( is a piece of software which is not too hard to configure and it also supports proxies out of the box. Ofcourse, it also has a client and a server side component and – because it uses SSL – you need certificates. So first of all, let's set up the certificates. GLPI-Wiki/wiki/doku.php?id=fr:config:ldap. Trace: » GLPI et les annuaires LDAP. Info / CyberTrack. Partager la connexion Internet avec d'autres machines locales. Tutoriel:un_simple_partage_nfs. Ce tutoriel propose une méthode qui se veut la plus simple possible pour accéder à distance aux documents enregistrés sur un ordinateur à partir d'un autre en utilisant le protocole NFS. Common Exploits - Penetration Testing Information. I have been playing with unquoted service paths/trusted paths the last few days and thought would write something up. Credit to Gavin Jones who introduced me to this issue, which to be honest I hadn’t heard of before and I normally only checked cacls and permissions of services.
What is the issue? Basically it is related to the path binary in services that are unquoted and contain spaces. If we look at the below Skype service you will see the path is quoted – “c:\program files (x86\” which is the correct way. How to make a tar archive. Installez le thème du Windows 8 sur Windows 7 en un temps record. Touche Arrêt défilement. [HowTo] Utilisation de la solution SYSPREP sous Windows Seven « Anthonix.fr – High Tech/Informatique : Tutoriels & actualité, insolite, geek ! Magnetic Window Edge. My top free Windows 7 add-ons. Dupliquer un virtual machine sur virtualbox. Bonjour , j'ai essayer la commande mais je reçoit le msg suivant : C:\Program Files\Sun\xVM VirtualBox>VBoxManage clonevdi "C:\Users\djili\.Virtual Box\HardDisks\Server_2008.vdi" "C:\Users\djili\Documents\virtualduplication\Seve r28Test.vdi" VirtualBox Command Line Management Interface Version 2.1.0 (C) 2005-2008 Sun Microsystems, Inc.
All rights reserved. Ndis usb android. Nmap 6.40 released: How to install and some examples using scripts. ~ Hacking while you're asleep. Step-by-Step: Installing SQL Server Management Studio 2008 Express after Visual Studio 2010 - Beth Massi - Sharing the goodness. Wire Scorpion. Tableaux. Mounting .VHD / .VDI file using Grub4dos. - Install Windows from USB. Share your PC's Internet with an Android Phone over USB. PXE Network Boot : TFTPD Configuration. PXE Server for Windows - Serva. L i v e l a b . d k - Products - Touchpad 2 MIDI. Distributed cracking with John the Ripper. How to share internet? Building a simple Beowulf cluster with Ubuntu. Parallel / distributed password cracking with John the Ripper and MPI.
Nice to Know – Get rid of all junk before Sysprep and Capture when creating a reference image in MDT « The Deployment Bunny. Invisibly Execute BAT File in the Background. Overview of Operation. Adamcaudill/Psychson. Calcul_matriciel_Cours.pdf. Multiplicateur de matrices. Log On Automatically at Startup. Disable Windows has detected a hard disk problem message in windows. How to Back Up and Restore NTFS and Share Permissions - Ask the Directory Services Team. John-André Bjørkhaug (@jabjorkhaug) Release 2.0 alpha 20141010 (oe.eo) edition · gentilkiwi/mimikatz. Is Anti-Virus Really Dead? A Real-World Simulation Created for Forensic Data Yields Surprising Results. AV Bypass « E-Spohn. How to Decrypt SSL and TLS Traffic using Wireshark. Process Injection Outside of Metasploit. Inquisb/shellcodeexec. Hash encapsulation to bypass AV. FauxCrypt. Tutorial – Application Fuzzing. Opensource.dyc.edu. Tunneling sessions via Plink. Creating Dynamic SSH Tunnel on Windows with Plink – Scriptable SSH Tunnels on Windows.
Problem with MSDTC. Open Source Tools by Joshua "Jabra" Abraham. Create a private "Dropbox" file host using BitTorrent Sync / iGARET. Writing buffer overflow exploits - a tutorial for beginners. C# - Install a .NET windows service without InstallUtil.exe. Hot Scripts - The net's largest PHP, CGI, Perl, JavaScript and ASP script collection and resource web portal. Recover MySQL root Password.
Taming the Stubborn Tomcat. Tunnelling Remote Desktop over SSH (PuTTY Settings) How To Use Netcat to Establish and Test TCP and UDP Connections on a VPS. Evade Windows Firewall by SSH Tunneling using Metasploit. Bypass new generation Firewalls with meterpreter and ssh tunnels. Quick notes – Get a meterpreter reverse shell through SSH tunnel. L'Internet (très) haut-débit dans les 745 communes du département de Seine Maritime. L'Internet (très) haut-débit dans les 745 communes du département de Seine Maritime. Fr/ipw2200. USING METASPLOIT SOCKS PROXY AUXILIARY MODULE OVER A METERPRETER SESSION. Google.