

GitHub - joeguilmette/ee-vvv-wordmove: A guide for local and production WordPress environments. Learning Ansible with Vagrant (Part 2/4) In this episode, we are going to play around with Ansible via four Vagrant virtual machines.

We will install Ansible from scratch, troubleshoot ssh connectivity issues, review configuration files, and try our hand at common commands. Series Recap Before we dive in, I thought it might make sense to quickly review what this episode series is about. In part one, episode #43, we looked at what Ansible is at a high level, basically a comparison of doing things manually versus using configuration management. In this episode, we are going to get hands on with Ansible, by look at patterns for solving common Sysadmin tasks.
Prerequisites If you have not already watched episode #42, where I gave a Crash Course on Vagrant, then I highly suggest doing that now. Vagrant Environment Let me show you what we are going to be building today by way of a couple diagrams. Our Vagrant environment is going to look like this. Supporting Materials Launching Vagrant Environment The README file Vagrantfile. Mastering Ansible. Mastering Ansible is a step-by-step journey of learning Ansible for configuration management and orchestration.
The course is designed as a journey through configuring a realistic application stack from the ground up. Instead of going page-by-page through the Ansible documentation, topics are ordered to align with the growing complexity of our application as we build it up and refactor it. In addition to the core concepts of configuration with Ansible, we spend time on building tools to help us maintain and troubleshoot our application. The goal is to have a workflow where all of the configuration and troubleshooting is done through ansible playbooks that can be committed to a repository and improved over time. Howto Make Script More Portable With #!/usr/bin/env As a Shebang. ByVivek GiteonMarch 6, 2007 last updated February 21, 2008 inDebian Linux, Linux, OpenBSD, OS X, Perl, RedHat/Fedora Linux, Shell scripting, Solaris, Suse Linux, Tips, Ubuntu Linux, UNIX You may have noticed that most shell and perl script starts with the following line: #!
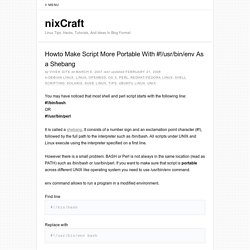
/bin/bash OR #! /usr/bin/perl However there is a small problem. Env command allows to run a program in a modified environment. Find line #! Replace with #! For example here is a small script: #! #! Now you don’t have to search for a program via the PATH environment variable. Share this on: OpenBSD manual pages. Ssh-keyscan — gather ssh public keys ssh-keyscan is a utility for gathering the public ssh host keys of a number of hosts.
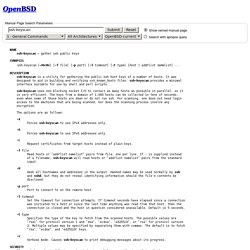
It was designed to aid in building and verifying ssh_known_hosts files. ssh-keyscan provides a minimal interface suitable for use by shell and perl scripts.ssh-keyscan uses non-blocking socket I/O to contact as many hosts as possible in parallel, so it is very efficient. The keys from a domain of 1,000 hosts can be collected in tens of seconds, even when some of those hosts are down or do not run ssh. For scanning, one does not need login access to the machines that are being scanned, nor does the scanning process involve any encryption. The options are as follows: Forces ssh-keyscan to use IPv4 addresses only.
Forces ssh-keyscan to use IPv6 addresses only. -c Request certificates from target hosts instead of plain keys. SSH login without password. Your aim You want to use Linux and OpenSSH to automate your tasks.

Therefore you need an automatic login from host A / user a to Host B / user b. You don't want to enter any passwords, because you want to call ssh from a within a shell script. How to do it First log in on A as user a and generate a pair of authentication keys. A@A:~> ssh-keygen -t rsa Generating public/private rsa key pair.
Now use ssh to create a directory ~/.ssh as user b on B. A@A:~> ssh b@B mkdir -p .ssh b@B's password: Finally append a's new public key to b@B:.ssh/authorized_keys and enter b's password one last time: