

Android Agony and SAFE Harbors. The battle for the one ruler of mobility has been ravishing the land for years.

As three powerful families of devices battle to usurp the others with larger screens, faster processors and more features, it has left the kingdom in great turmoil on who they should trust as the most benevolent ruler of productivity. Join Fiberlink as Medieval Mobile MaaSters for Apple, Android and Windows clash to determine which device family will sit upon the silicon throne.
Apple: Lord Andrew Clarke: Like the Lannisters, Apple is the current leader of Enterprise mobility with the most devices activated in business and schools. With its beloved features, apps, usability, and expanding device options, the iOS platform seems fit to rule for years to come. But it remains to be seen just how far Apple can extend its empire across the continents. Windows: Squire Sergiy Mimkha: Windows like the Starks has taken quite a few battle scars in the battle for mobility. Mobile Device Management (MDM) Security Response Publications, Internet Security Threat Report. Symantec Security Response is a worldwide team of security engineers, threat analysts, and researchers who develop a variety of content on the latest threats that impact organizations and end users.

Archives 2014 Internet Security Threat Report, Volume 19 The Internet Security Threat Report provides an overview and analysis of the year in global threat activity. The report is based on data from the Symantec Global Intelligence Network, which Symantec's analysts use to identify, analyze, and provide commentary on emerging trends in the dynamic threat landscape. Overview and Analysis 98 pages, 11.5 MB (PDF) Guide for Apple App Store submissions. Before you start to package your AIR app for submission, make sure you take care of some key considerations to ensure your users have the best experience possible.
These considerations fall generally into two categories: performance and usability. To make sure you have built a high-performing app, test your application on a variety of devices. Performance Typically, the iPod touch is faster than an iPhone in the same class of hardware. For example, the iPod touch 32GB and iPod touch 64GB are faster than the iPhone 3GS, even though they're in the same class of hardware.
FOR ENTERPRISE-Solutions-Security. SAMSUNG. Login. Login. Login. Activate mobile devices - Google Apps Help. Présentation de Mobile Management - Centre d'aide Google Apps. MaaS360 by Fiberlink. Review app permissions - Google Play Help. Manage Android devices - Google Apps Help. Apps Device Policy - Aplikacje Android w Google Play. Menedżer urządzeń Android - Aplikacje Android w Google Play. Menedżer urządzeń Android - Aplikacje Android w Google Play. AirWatch Mobile Device Management.
AirWatch offers one of the more comprehensive enterprise mobile management solutions that scales across cloud and on-premises deployments.
The platform supports containerization through it's Workspace feature along with a "dual-persona" option that separates the personal and corporate resources on the devices. AirWatch was recently acquired by VMware and identified as a leader in the enterprise mobility management space in Gartner's magic quadrant. 1. Integration & Compatibility AirWatch integrates with AD/LDAP, Certificate Authorities, Public Key Infrastructures, email infrastructures and other enterprise systems both in cloud and on-premises deployments. Security Overview. Introduction Android is a modern mobile platform that was designed to be truly open.
Android applications make use of advanced hardware and software, as well as local and served data, exposed through the platform to bring innovation and value to consumers. To protect that value, the platform must offer an application environment that ensures the security of users, data, applications, the device, and the network. Apps Device Policy - Aplikacje Android w Google Play. Bring Your Phone to Work Day: Managing Android Devices With Google Apps. Today in Tokyo, more than 600 IT leaders from across Japan are coming together with Google and 18 of our partners at Google Enterprise Day.
It’s our annual event dedicated to discussing trends in enterprise technology and how businesses can use cloud technologies to increase productivity and innovate more quickly. This year, one of the hottest topics is mobile computing and how companies can allow employees to use their personal phones and tablets at work without compromising corporate security. With over 200,000 devices activated each day, Android is seeing rapid adoption, and today we are launching new administrative controls that make it possible to securely manage these devices in the Google Apps environment.
Putting Android to work for your business. With more than 300,000 devices activated per day globally, Android is seeing rapid adoption in the post-PC era.
Android works quite well with Google Apps, but we’re working to make it an excellent choice for both end-users and IT at businesses and schools. Over the last year for instance, we helped IT administrators manage Android straight from the browser, and we introduced features such as Priority Inbox view in Gmail for Android and the ability to edit Google Docs on the go. Low Level View of Android System Architecture.
Security and Hacking apps for Android devices - InfoSec Institute. Now days, smartphones and tablets are most the popular gadgets.

If we see recent stats, global PC sale has also been decreasing for the past few months. The reason behind this is that people utilize tablets for most of their work. Android Security related tools. Brief Tour about Android Security. Manage Android devices - Google Apps Help. New Google Apps Mobile Management features for Android amp up productivity and security. Posted by Clayton Jones, Product Manager, Google Enterprise Bring your own device (BYOD) is no longer just a trend — it’s how business gets done.
With thousands of mobile applications to choose from and an increasing number of websites optimized for mobile, today’s employees can work whenever and wherever they choose. It also means IT organizations now have the dual challenge of both helping employees be more productive and protecting corporate data. Official Google for Work Blog: Increasing security and productivity for iOS devices. Authenticator. Android Developers Blog. Codelines, Branches, and Releases.
The Android Open Source Project (AOSP) maintains a complete software stack to be ported by OEMs and other device implementors and run on their own hardware.
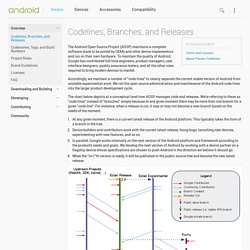
To maintain the quality of Android, Google has contributed full-time engineers, product managers, user interface designers, quality assurance testers, and all the other roles required to bring modern devices to market. Accordingly, we maintain a number of "code lines" to clearly separate the current stable version of Android from unstable experimental work. We roll the open source administration and maintenance of the Android code lines into the larger product development cycle. The chart below depicts at a conceptual level how AOSP manages code and releases. We're referring to these as "code lines" instead of "branches" simply because at any given moment there may be more than one branch for a given "code line".
At any given moment, there is a current latest release of the Android platform. Interfaces. Android provides you with the freedom to implement your own device specifications and the drivers to support them. The hardware abstraction layer (HAL) gives you a standard way to create software hooks in between the Android platform stack and your hardware. In addition, the Android operating system is open-sourced to help you through your device's bringup.
To ensure that your devices maintain a high level of quality and offers a consistent experience for your users, they must must also pass the tests in the compatibility test suite (CTS). CTS ensures that anyone building a device meets a quality standard that ensures apps run reliably well and gives users a good experience. For more information, see the Compatibility section. (99+) Android Security Discussions. 5.0 APIs. API Level: 21 Android 5.0 (LOLLIPOP) offers new features for users and app developers. This document provides an introduction to the most notable new APIs. If you have a published app, make sure to check out the Android 5.0 Behavior Changes that you should account for in your app. These behavior changes may affect your app on Android 5.0 devices, even if you are not using new APIs or targeting new functionality. For a high-level look at the new platform features, instead see the Android Lollipop highlights.
Start developing To start building apps for Android 5.0, you must first get the Android SDK. Google Apps Free Trial Sign Up. Google Apps for Business Free Trial Mail, Calendar, Drive, Docs, and so much more Google Apps is a cloud-based productivity suite for your business that helps you get work done from anywhere on any device. The ViWO Trial Difference. Bring Your Own Device Part 2: Mobile Management (MDM) With Google Apps. This is part 2 of 2 of our series on BYOD. You can access Part 1 here. In the first part of our BYOD series, What Is BYOD?
, we explained what this phenomenon is all about, where it came from, and what the benefits and challenges are. On the challenges side, many of these concerns revolve around security and compliance. Fortunately, a new breed of software called “Mobile Device Management Software” (or MDM) has emerged to help administer and mitigate many of the issues. Configure mobile device settings - Google Apps Help. WiFi Network settings allow you to automatically add a configured network or networks to managed Android devices and iOS devices if they are setup using new native MDM. Manage Android devices - Google Apps Help. Mobile Management overview - Google Apps Help. Android Security for Embedded Systems. Android remains a popular operating system, but it also remains the most targeted mobile device out there. HCE vs embedded secure element: comparing risks (part I) Evaluation Pathway for Mobile Devices: ASD Australian Signals Directorate.
Pricing & Features. Security Management. CA Technologies. Connexion : comptes Google. Cloud_Admin. After gaining U.S. government approval, Samsung Knox security for Android found to be "completely compromised" [u] Samsung KNOX. Common Access Card. The Common Access Card, also colloquially referred to as the CAC (often called CAC card, due to what is informally known as RAS syndrome), is a smart card about the size of a credit card.[1] It is the standard identification for active-duty military personnel, Selected Reserve, United States Department of Defense (DoD) civilian employees, and eligible contractor personnel.[1] It is also the principal card used to enable physical access to buildings and controlled spaces, and it provides access to defense computer networks and systems.[1] It also serves as an identification card under the Geneva Conventions (esp. the Third Geneva Convention).
The CAC satisfies two-factor authentication: something that belongs to the user, and something only known to the user. Cloud-User. Cloud_Admin. Cloud_Admin. KNOX EMM Quick Start Guide. [KNOX 2.0] User Guide (Enterprise) Use and manage mobile devices - Google Apps Help. Configure mobile device settings - Google Apps Help. Android Device Manager - Accounts Help. Sovelluksien tarkistaminen ja valitukset - Android Developer Ohjeet. Samsung Knox™ on Galaxy S®5 with MaaS360 for Business. As cybercrime outstrips the information security profession’s ability to tackle it, the need for increased collaboration between enterprises, governments and organizations has never been more important. Actionable intelligence on current and future attacks is critical if organizations are going to be able develop effective risk mitigation tactics.
The challenges to open collaboration are significant however, as organizations fear losing their competitive advantage, and governments fear national security. The lack of incentives to share information is also an inhibitor, as is the lack of a framework and common terminology. Whilst many informal information sharing networks exist between peers and colleagues, this has limited value for the sector as a whole.
As cybersecurity risks increase, how can governments, enterprises and organizations work together to share information that will arm them with actionable intelligence that will enable them to tackle their cyber-adversaries? The truth about Samsung Knox for Android security. KNOX Workspace. Google, Samsung integrate Knox into Android, eye enterprise gains. Google stops ignoring enterprise, adds EMM to Android. Administrative Systems. Mobile Device Management (MDM) Will MDM Work on My Android? Android Device Manager - Accounts Help.
Protect against harmful apps - Accounts Help. Android Developer Help. Essentials for a Successful App. Mobile Management overview - Google Apps Help. Bring Your Own Device Part 2: Mobile Management (MDM) With Google Apps. Server Help. Mobile security. Mobile Applications: How Safe is your information? iPhone Configuration Utility 3.5 for Mac OS X. Configurator Help. Push Certificates Portal. Configuration Profile Reference: Configuration Profile Key Reference. Prepare for the Security Implications of the Digital Workplace. iOS restrictions - iOS Deployment Reference. Profile Manager - iOS Deployment Reference. Use Profile Manager - Profile Manager Help. About profiles and payloads - Profile Manager Help. iOS restrictions - iOS Deployment Reference. iOS restrictions - iOS Deployment Reference. Configurator - iOS Deployment Reference.
AirWatch TV. White Papers. White Papers. AirWatch TV. AirWatch Free Trial. Magic Quadrant for Mobile Device Management Software. Magic Quadrant for Mobile Device Management Software. Systems, Inc. Mobile Device Management, MDM - ManageEngine Desktop Central. Mobile Device Management, MDM - ManageEngine Desktop Central. MobileIron. MobileIron.