

RecStudio Decompiler Design - Introduction. Decompilation is a form of reverse engineering of computer programs.

Its goal is to convert a compiled binary file into a source file. One may want to do this for several reasons, such as to understand how a program works, or to try to modify a program to enhance it or fix a bug. Decompilation has been around for many years, probably ever since people started to compile programs from high-level languages to lower-level formats such as assembly and machine code. Several attempts have been conducted at writing binary executable decompilers. This page has some examples. There are even more decompilers available for managed environments that use byte-code, like Java and C#. In these pages we’ll focus on decompilation of binary executables, or from machine code to source code, since this is much more difficult than decompiling Java byte-code or C#.
Several languages and compilers can produce machine code, including some Java, C# and Visual Basic compilers. RecStudio Decompiler Design - Reverse Tools. Prev: Forward Engineering Tools Even during development, programmers regularly use reverse engineering tools to verify the correctness of their program.
The most used tool is clearly the debugger. Debuggers are the best reverse engineering tool, since they allow the step by step execution of the program and the inspection of the program’s variables. Whether a debugger is used to debug the original source code or machine code depends on whether debugging information is available to the debugger.
Typically debugging information is generated by the compiler via a switch (such as –g for gcc), and is passed through by the assembler and linker to the debugger. While a debugger can do run-time or “dynamic” analysis of the target program, the other tools can only do “static” analysis. Disassembling is one of the features of debuggers, but it can also be performed by a stand-alone tool, a disassembler. Smarter disassemblers are able to provide more information about a specific instruction. Reverse Engineering Resources. Object File Formats. Reverse Engineering Resources - Decompilers. The Decompilation Wiki. Home SurveysTransformationReengineeringDSLDomain EngineeringDecompilationGenerative Progr.CollectionsCategoriesSystemsConferencesPeopleCompaniesPapers Page More ...
Web Wiki. REference Debugger Module Description. A debugger for a generic processor is made up of several components, some of them completely independent of the target processor and the target environment, others very specific.

It is useful to separate the description of the two types so that the effort to develop or port each one can become clearer. The following components can be considered independent of the host and target environment, and can be thought of as the core of the debugger. REference Debugger. Welcome to the REference Debugger (RED).

This page is dedicated to debugger technology. Surprisingly, there is not much information on the Internet on the internal working of debuggers, so I decided to share my knowledge about the subject in these pages. If you are curious about how debuggers work, or you want to write your own debugger, here you will find information, algorithms, and a reference debugger implementation from which you can derive your own debugger. You may wonder who needs another debugger when gdb is already available for many different platforms and processors. The problem is that gdb is so big and its code has evolved over the years that it has become difficult to understand for people who are not already familiar with debugger technology. The goal of the RED project is to keep the architecture simple and understandable, so that people can learn from it, and possibly extend it.
Decompiler Rec Test. Program-Transformation.Org: The Program Transformation Wiki Some simple tests were performed on REC 1.6 for Linux.
Fibo/286 This test file is the same one used to test the 286 decompilers (dcc and Exe-2-C). It's pretty impressive that REC can handle this old code at all. Original C source: The disassembly for the fib function is /* Procedure: 0x0000025B - 0x0000028A * Argument size: 4 * Local size: 0 * Save regs size: 4 */ L0000025B(A4) /* unknown */ void A4; { if(A4 <= 2) { ax = 1; } else { (save)L0000025B(A4 - 1); dx = L0000025B(A4 + 65534); (restore)ax; ax = ax + dx; } } As with Exe-2-C, push and pop are explicit (as save and restore), registers are still visible, and no attempt is made to join the semantics of individual instructions. Here is the code for main: It has not recognised the library functions printf, scanf, and exit. Fibo/Elf. Reverse Engineering Compiler. Program-Transformation.Org: The Program Transformation Wiki REC, a Reverse Engineering Compiler by Giampiero Caprino (gcaprino@katamail.com), is a portable decompiler which supports a variety of different input binary files and produces a C-like representation as output.
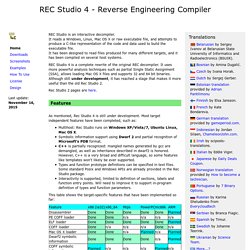
Source processors supported at present include: Intel 386, Motorola 68000, MIPS R3000 and Motorola PowerPC. Version 1.6 also supports SPARC. Amongst the source binary file formats accepted are: Unix Elf, Unix COFF, Windows PE, Linux and SunOS AOUT, PlayStation PS-X, and raw binary data. As of mid 2005, the author appears to be back working on this decompiler, and has produced a Windows GUI called RecStudio. REC started as a workbench to test compiler related algorithms. Download REC Studio. Read the License for important information regarding the use of Rec Studio.
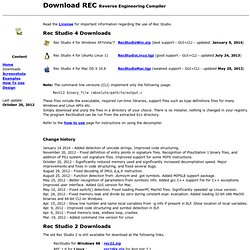
Rec Studio 4 Downloads Note: The command line versions (CLI) implement only the following usage: RecCLI binary_file /absolute/path/to/output.c These files include the executable, required run-time libraries, support files such as type definitions files for many Windows and Linux APIs etc. Simply download and unzip the files in a directory of your choice. REC Decompiler Home Page. Several other decompilers are available from various sources.
Look at my reverse engineering page for a list. Rather surprisingly, the internal architecture of a decompiler is very similar to that of a compiler. High-quality literature exists for both.