

idcube identificaton systems
Idcube is uniquely positioned among leading provider of access control & security solutions.
What is Anti-passback? - IDCUBE. In an access control system, the anti-passback feature plays the role of that invisible watch guard who stops anyone who tries to obstruct a specific access sequence.

The terms anti-piggybacking, anti-tailgating, anti-buddy-punching, and anti-passback demonstrate the same concepts. In this system, a distinctive pattern (in-out-in-out-in-out) applies to both the entry and exit readers that must be followed by an individual user to gain unhindered entry and exit. If by any chance this sequence is disturbed/ misused (in-in-out), the system initiates an automatic response mechanism as per the Anti-passback rule configuration. Let’s have a look at the different types of anti-passback rules for various response mechanisms: Let us understand these rules in brief- Real Anti-passback Real Anti-passback can be differentiated into two parts, as described below: a. Entry and exit readers are set in a way to deter any user from gaining access if the specified pattern is disturbed.
B.
Making PACS Unbreachable - IDCUBE. Security of an organization commonly comprises three critical systems – Physical Access Control System (PACS), Video Surveillance, and Logical Access Control.

Physical access control is the first line-of-defense against security breaches, whereas video surveillance is required more for root cause analysis post-incident. Moreover, intrusion into information-systems occurs generally from within the facility. Therefore, one must ensure that PACS is implemented in the most effective way to stop potential security breaches. In this blog, we discuss several pointers to create a more secure web of PACS to make it unbreachable in the real sense, in opposition to the threats & vulnerabilities (as discussed in “How to hack Physical access control system (PACS)“). 1. To ensure better security, install all the controller devices and the corresponding cabling in a way or an area invisible and inaccessible to the public.
What is Open Supervised Device Protocol (OSDP)? - IDCUBE. What triggered the security specialists to introduce OSDP?

Continuous advancements in physical access control technology seek evolvement against threats, vulnerabilities, and updates in the security protocols. One of the striking changes that occurred, in this case, can be referred to as Open Supervised Device Protocol (OSDP). OSDP is the new card reader connection standard that has dethroned the legacy protocol known as Wiegand technology.
All the significant industry manufacturers are endorsing it since its inception in 2011 by the Security Industry Association (SIA). Wiegand technology, running for more than 40 years, lacks in many technical fields that made it mandatory for the experts to search for a better alternative. Moreover, Wiegand is unsupervised, holds limited distance usage, and the wires are supposed to always remain in good shape without any induced electrical interference.
How to hack an Access Control System? - IDCUBE. The physical access control system (PACS) strengthens enterprise security in an unprecedented way.

However, hackers and bad guys try to gain unauthorized access to the facility by manipulating the system vulnerabilities and cause damage. The blog highlights some of the most commonly exploited vulnerabilities that may weaken the security of an enterprise. Following is the summary of the crucial dangers to PACS from the gate-crashers: Card Cloning: Cloning of RFID cards or Card Serial Number (CSN) simulation to gain unauthorized access is the most common way to hack an access control system.Wire-Tampering: Exposure of lock cables or control cables to unsafe areas may lead to cable tampering for unauthorized access.Reader Replacement (Scenario 1): Standalone reader-cum-controller is one of the most significant security risks to a facility.
How to tackle these problems effectively?
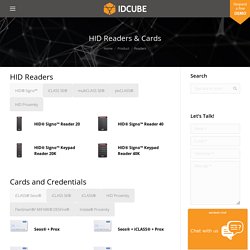
Readers - IDCUBE. Skip to content HID Readers HID® Signo™ Keypad Reader 20K HID® Signo™ Keypad Reader 40K HID® iCLASS SE® Express R10 HID® multiCLASS SE® RPK40 HID® multiCLASS SE® RPKL40 HID® multiCLASS SE® RMP40 HID® multiCLASS SE® RMPK40 HID® pivCLASS® Biometric Reader HID® Proximity MiniProx® Hazardous Location 5365 HID® Proximity ThinLine II® 5395 HID® Proximity ProxPro® 5355 HID® Proximity ProxPro® with Keypad 5355.
Vehicle Access Management. Visitor Management System. EzVISIT is a new age enterprise visitor management system ensuring security, convenience, process automation and compliance.
These days convenience is defined by mobility, agility and convergence. ezVISIT offers intuitive interfaces over a mobile and a web browser for pre-registration of a meeting ranging from a single visitor to a group or large audience at a conference. The ezVISIT lobby application comes as a self-service kiosk to service visitor with an easy enrollment process for a welcoming user experience. The systems maps with organizations security processes to enroll various visitors ranging from guests, vendors, contractors, job candidates and more. Each visitor type can have a different process cycle, Inclusive of meeting request, possible approval(s), capturing visitor details at arrival, authorization, notification, badge printing, meeting sign off and check out.
Visitor Management Architecture. Video Management System with Analytics & License Plate Recognition. Enterprise Access Control and Time & Attendance Software - IDCUBE. Time Attendance System - IDCUBE.