

Test: Samsung SSD 840 EVO 250 GB. Hardver 09.08.2014 12:56.

What is a Center of Excellence. Continuing a series of posts addressing some of the lessons and take aways from recent experience in establishing Centers of Excellence.
I’ve never really liked the term. Sounds so haughty. I prefer ‘Competency or Capability Center’ or pick any another term you like. But, ‘Center of Excellence’ seems to be what has stuck in the business world, so we’ll go with it here. Definition: Whatever you call them, a Center of Excellence (CoE) should, at a most basic level consist of: A team of people that promote collaboration and using best practices around a specific focus area to drive business or customer-valued results. Startup Engineering. About the Course Spiritual sequel to Peter Thiel's CS183 course on startups.
Bridges the gap between academic computer science and production software engineering. Fast-paced introduction to key tools and techniques (command line, dotfiles, text editor, distributed version control, debugging, testing, documentation, reading code, deployments), featuring guest appearances by senior engineers from successful startups and large-scale academic projects. Over the course of the class, students will build a command line application, expose it as a web service, and then link other students' applications and services together to build an HTML5 mobile app.
General principles are illustrated through modern Javascript and the latest web technologies, including Node, Backbone, Coffeescript, Bootstrap, Git, and Github. Course Format. Coded with love (and javascript: nodejs, angularjs and mongodb) Angustore - Responsive Shopping Cart. Netgear and Linksys DSL routers 'fix' does nothing about the backdoor, merely hides it says Arstechnica report. 132 Shares117411000×132 Shares Eloi Vanderbeken, a security researcher from synacktiv.com had discovered a backdoor in several models of Linksys, Cisco and Netgear Wi-Fi DSL modems that would grant admin access to the attacker along with the ability to reset the router's configuration.
After Vanderbecken published his findings and several others corroborated his results in January 2014, the modem manufacturers like Netgear and other vendors published a new version of the firmware that was supposed to close the back door. Now Vanderbeken has found that the firmware released by the vendors is just a camouflage. As per a report by Arstechnica, the new firmware does not 'fix' the backdoor. Hack. Microweber CMS - An open source CMS with Ecommerce support. To the user's satisfaction, there is a whole wide world of different CMS, all suitable for different needs.

You can go for the giants like Wordpress or Joomla or pick one of the rising forces - Shopify, Squarespace or others. Microweber CMS fills a hole in the current technological ecosystem, aimed at delivering a light software that is perfect for all end-users lacking the technical knowledge needed for complicated website building. Microweber is free, open source, and operates on the innovative Drag & Drop technology. C# From a Java Developer's Perspective. The C# language is an object-oriented language that is aimed at enabling programmers to quickly build a wide range of applications for the Microsoft .NET platform.
The goal of C# and the .NET platform is to shorten development time by freeing the developer from worrying about several low level plumbing issues such as memory management, type safety issues, building low level libraries, array boundschecking , etc. thus allowing developers to actually spend their time and energy working on their application and business logic instead. As a Java developer the previous sentence could be described as "a short description of the Java language and platform" if the words C# and the .NET platform were replaced with words Java and the Java platform. The C# Programming Language for Java Developers. Database Refactoring Patterns.
Four Layers of JavaScript OOP. The Most Advanced Responsive Front-end Framework from ZURB. Bomb that can destroy your Linux Box. In computing, a fork bomb (also called rabbit virus or wabbit ) is a denial-of-service attack whereby a process continually replicates itself to deplete available system resources.

Best Terminal alternatives for Linux systems Fork bombs operate both by consuming CPU time in the process of forking, and by saturating the operating system's process table. A basic implementation of a fork bomb is an infinite loop that repeatedly launches the same process. In Unix-like operating systems, fork bombs are generally written to use the fork system call. As forked processes are also copies of the first program, once they resume execution from the next address at the frame pointer, they also seek to create a copy of themselves; this has the effect of causing an exponential growth in processes. 3 Simple Steps to Opencart Optimisation and Improving SEO (Opencart v 1.5.4.1) 1) Minify / gzip your css, javascript and jquery files - increases 40-50% of Pagespeed points & reduces almost 40-50% of your 1st request data loading size and time 2) Enable caching - increases around 5-15% of pagespeed points and almost 40-50% of your 2nd request onwards load time 3) Optimize images / image size - increases 5-15% of pagespeed points and almost 20 - 30% of your 1st request data loading file size and time 1) Minify CSS, javascript and other files using gzip This is the most important part of your opencart optimisation. it reduces almost 300KB file size making your pagespeed points up by almost 40% - 50%.
My website is hosted on Apache and hence the below code in the .htaccess file does the gzip process automatically. 2) Enable caching for the images and files such as Javascript, css etc. The 2nd important part is to cache the images, and the common files required such as CSS, Javascript etc. . # Set up caching on media files for 5 weeks <FilesMatch "\. CoryFoy/DotNetKoans. Учебные курсы Часть 4 [2010-2013] PCRec [ENG] Software PracticesSoftware Practices\Advanced Unit Testing\Software Practices\Agile Team Practices with Scrum\Software Practices\Automated Testing End to End\Software Practices\Automated Testing for Fraidy Cats Like Me\Software Practices\Brownfield Application Development\Software Practices\Building Extensible Applications with MEF\Software Practices\Continuous Integration\Software Practices\Continuous Testing with NCrunch\Software Practices\Design Patterns Library\Software Practices\Getting Started With Jenkins Continuous Integration\Software Practices\Inversion of Control\Software Practices\Kanban Fundamentals\Software Practices\RhinoMocks Fundamentals\Software Practices\SOLID Principles of Object Oriented Design\Software Practices\Test First Development - Part 1\Software Practices\Test First Development - Part 2\ Source ControlSource Control\Introduction to SVN\Source Control\Mercurial Fundamentals\Source Control\Team Foundation Server 2010 Version Control\
![Учебные курсы Часть 4 [2010-2013] PCRec [ENG]](http://cdn.pearltrees.com/s/pic/th/pluralsight-2010-pcrec-torrent-78914351)
Browserver: a node.js HTTP server in your browser. Browserver: a node.js HTTP server in your browser. Architecting for the Cloud. The biggest difference between cloud-based applications and the applications running in your data center is scalability.
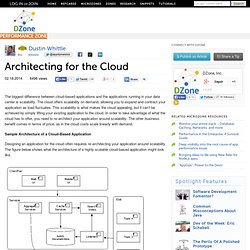
The cloud offers scalability on demand, allowing you to expand and contract your application as load fluctuates. This scalability is what makes the cloud appealing, but it can’t be achieved by simply lifting your existing application to the cloud. In order to take advantage of what the cloud has to offer, you need to re-architect your application around scalability. The other business benefit comes in terms of price, as in the cloud costs scale linearly with demand.
Sample Architecture of a Cloud-Based Application Designing an application for the cloud often requires re-architecting your application around scalability. The Client Tier: The client tier contains user interfaces for your target platforms, which may include a web-based user interface, a mobile user interface, or even a thick client user interface. Use of Assertions. Assertions are great because they: support better testing,make debugging easier by reducing the distance between the execution of a bug and the manifestation of its effects,serve as executable comments about preconditions and postconditions,can act as a gateway drug to formal methods. Assertions are less than great because they: slow down our code,make our programs incorrect — when used improperly,might trick some of us lazy programmers into using them to implement error handling,are commonly misunderstood. Configuring the package.json and Gruntfile.js files. Hi, my name is Mike McLin and in this video I am going to talk about the 2 files that are required for Grunt Task Runner to function.
The first is the package.json file which we’ll use to describe metadata about our project, like the name, version number, etc. We will also use this file to load the necessary plugins required by Grunt. From there I’ll discuss the second file required for Grunt to function, which is the Gruntfile.js. This is your main configuration file, and where we’ll spend most of the time in this video. The Gruntfile.js is where everything really happens. Creating a package.json file. Optimizing Your Workflow with Grunt - Bocoup. Learn about tools and practices to improve your development workflow so that you can be more confident and efficient in how you build web applications. Is this class right for you? This class is intended for the intermediate or advanced web developer who is interested in improving their process. Comprehensive beginner and advanced jQuery JavaScript and HTML5 training onsite and at The Bocoup Loft - Bocoup.