

Our Courses. InfoSec-Policy-and-Standards-Program-placemat.pdf. GlobalSecurity.org - Reliable Security Information. Center for Internet Security - Multi-State Information Sharing and Analysis Center. Status overview. Cyber Security and Information Systems Information Analysis Center. Cyber Security and Information Systems Information Analysis Center. CJCS Manuals. Www.dtic.mil/cjcs_directives/cdata/unlimit/m651001.pdf. Global Website Fingerprinting. European Centre for Information Policy and Security. Security Affairs. Same Origin Method Execution (SOME) is a new technique of attack against website presented by Ben Hayak, researcher at Trustwave, at Black Hat Europe in Amsterdam.

The Same Origin Method Execution (SOME) attack method is related to JavaScript Object Notation with padding (JSONP) implementation, it allows a bad actor to impersonate the targeted user, and most concerning aspect of the attack is that the there is no need for user interaction if malicious code is served through a classic malvertising campaign.
Be aware, if a domain is vulnerable to the attack, all its pages will result vulnerable. 4aa5-0501enw. Building-Maturing-and-Rocking-a-Security-Operations-Center-Brandie-Anderson. Central Michigan University. Everything is Vulnerable. Set up your own Pen-testing/Hacking Lab Network using a Single System. The only thing to look for is your systems hardware configuration.

You should have minimum 2 GB RAM but it is highly recommended to use 3 GB RAM for a 32 bit operating system. We will be using Oracle VirtualBox in this tutorial. You can download virtualbox from this link [Reference 1]. Once you have installed Vbox, the next step is to download the Extensions pack. You can get it from this link [Reference 2] Once you have followed these initial steps, you are half done. Windows Tools For Penetration Testing. Most penetration testers are using either a Mac or a Linux-based platform in order to perform their penetration testing activities.However it is always a good practice to have and a Windows virtual machine with some tools ready to be used for the engagement.The reason for this is that although Windows cannot be used as a main platform for penetration testing some of the utilities and tools can still help us to extract information from our windows targets.So in this post we will see some of the tools that we can use in our windows system.

HashCheck Shell Extension The HashCheck Shell Extension makes it easy for anyone to calculate and verify checksums and hashes from Windows Explorer. In addition to integrating file checksumming functionality into Windows, HashCheck can also create and verify SFV files (and other forms of checksum files, such as .md5 files). Netcat. 2013 Honeynet Project Workshop. Historical CERT Documents. Home — Risk I/O Vulnerability Management. Set up your own Pen-testing/Hacking Lab Network using a Single System.
Online BackTrack Security Training by Offensive Security. The Creators of BackTrack have developed training that will take you through all aspects of a penetration test.

Whether you are a seasoned penetration tester or just starting off, we have a course that can help you take your skills to the next level. Our online courses are designed to give you flexibility to work at your own pace. Our flagship course, Penetration Testing With Kali (PWB) will open your eyes to the skills needed to perform a penetration test from A to Z. After that you can move on to Cracking the Perimeter (CTP) – which focuses on exploitation using many of the skills you learned in the PWB class. Powerful ‘Flame’ cyberweapon tied to popular Angry Birds game. May 28, 2012: A screenshot from researchers at Kaspersky Labs shows the code behind Flame, called "the most sophisticated cyber weapon yet unleashed.

"Kaspersky Labs The most sophisticated and powerful cyberweapon uncovered to date was written in the LUA computer language, cyber security experts tell Fox News -- the same one used to make the incredibly popular Angry Birds game. LUA is favored by game programmers because it’s easy to use and easy to embed. Flame is described as enormously powerful and large, containing some 250,000 lines of code, making it far larger than other such cyberweapons. Yet it was built with gamer code, said Cedric Leighton, a retired Air Force Intelligence officer who now consults in the national security arena. “The people who developed the malware … found an ingenious way to use a code not part and parcel of a hacker’s normal arsenal, and that made it harder to detect,” he told Fox News.
“Flame is a cyberespionage operation,” he told FoxNews.com.
BASH Programming - Introduction HOW-TO: Variables. NextPreviousContents 5.

Variables You can use variables as in any programming languages. There are no data types. A variable in bash can contain a number, a character, a string of characters. You have no need to declare a variable, just assigning a value to its reference will create it. 5.1 Sample: Hello World! #! Line 2 creates a variable called STR and assigns the string "Hello World! " 5.2 Sample: A very simple backup script (little bit better) #! Projects - *ORA. Overview | People | Sponsors | Publications | Hardware Requirements | Software | Training & Sample Data *ORA is a dynamic meta-network assessment and analysis tool developed by CASOS at Carnegie Mellon.
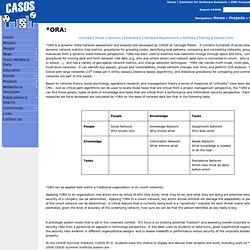
It contains hundreds of social network, dynamic network metrics, trail metrics, procedures for grouping nodes, identifying local patterns, comparing and contrasting networks, groups, and individuals from a dynamic meta-network perspective. *ORA has been used to examine how networks change through space and time, contains procedures for moving back and forth between trail data (e.g. who was where when) and network data (who is connected to whom, who is connected to where …), and has a variety of geo-spatial network metrics, and change detection techniques.