

Run A Tor Relay On Ubuntu Trusty. If you’ve seen the Tor Challenge, you may be wondering how hard it really is to run a relay on one of your spare machines… It’s not hard at all!

You can probably get up and running in less than half an hour. The following instructions detail how to set up a middle relay on a fresh Ubuntu 14.04 (Trusty), but should apply to most Ubuntu configurations. Also, the official documentation covers every topic you can possibly think of. Anyways, let’s get to it. Installing OpenNTPD Tor is pretty sensitive to clock skews, so the first thing we are going to do is install the openntpd package on the system in order to keep the clock in sync: $ sudo apt-get install openntpd The default configuration worked perfectly for me, but feel free to review it at /etc/openntpd/ntpd.conf. We can check our clock skew by running something like this: The offset is well under a second, so we are good. Installing Tor We’ll fetch Tor from the official package repository then. Everything looks good, so let’s do this:
Double Double Toil and Trouble — Stem 1.4.1 documentation. Relays - Run Tor in the background via the shell - Tor Stack Exchange. Upstart (Ubuntu, Chrome OS, Fedora 9–14), or sysvinit (Debian) From your previous question I get that you are using Ubuntu as the operating system.
Untitled. Kernel - How can I give a user permission to open low port numbers? - Ask Ubuntu. Doc/OperationalSecurity. Encrypt Storage and Swap Space ¶ Make sure that any sensitive files are stored on an encrypted filesystem and that file permissions are set correctly.
With a Tor server, the only sensitive information is the server's private key (located in /usr/local/etc/tor/keys on Unix/Linux platforms; readable only by owner). Additionally, swap space on the machine should be encrypted if your operating system has such an option. Globe 0.4.8. Atlas. Atlas is a web application to discover Tor relays.
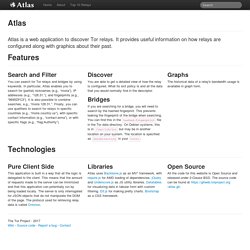
It provides useful information on how relays are configured along with graphics about their past. Search and Filter You can search for Tor relays and bridges by using keywords. In particular, Atlas enables you to search for (partial) nicknames (e.g., “moria”), IP addresses (e.g., “128.31.”), and fingerprints (e.g., “9695DFC3”).
Home - ReThinkVPS. Doc/TorExitGuidelines. These guidelines are meant to give you a quick introduction into the business of running your own exit relay.
Additional resources can be found at the end of this article. NOTE: This FAQ is for informational purposes only and does not constitute legal advice. Our aim is to provide a general description of the legal issues surrounding Tor exit relaying. Different factual situations and different legal jurisdictions will result in different answers to a number of questions. Therefore, please do not act on this information alone; if you have any specific legal problems, issues, or questions, seek a complete review of your situation with a lawyer licensed to practice in your jurisdiction.
Support ¶ If you are running an exit, or are thinking about it, you should subscribe to the Tor-Relays list. Hosting ¶ Abuse:templates - Wiki. Reply to Abuse (general) Hi $TO$, I am very sorry to hear that.
The IP you quote hosts a Tor exit node (open relay). I can offer you to block specific destination IPs and ports, but the abuser doesn't use our relays specifically; he/she will just be routed through a different exit node outside of our control instead. Tips for Running an Exit Node with Minimal Harassment. Updated 06/30/2010: Mention Reduced Exit Policy, ISP Shopping Tips, and Abuse Response Templates Updated 08/30/2010: Update exit policy with svn, git, hg, Kerberos, remote admin panels, IRC, others Updated 01/12/2011: Suggest creation of LLC for large exit nodes, provide links to ARIN forms and process.

Updated 02/25/2015: Torservers.net abuse templates URL has changed. I have noticed that a lot of new exit nodes have recently appeared on the network. This is great news, since exit nodes are typically on the scarce side. However, I want to make sure that these nodes stay up and don't end up being shut down due to easily preventable abuse complaints. 1. Pick an ISP you can trust, and let them know exactly what is going on. In a follow up email, you should explain Tor to them, and why it is important to the Internet, the world, and to you, their potential customer.
If your ISP does not approve, all is not lost: you can look into running a middle node, or a much less visible bridge node. Chilling Effects. Tor: Myths and Facts. Tor Challenge. FAQ written by the Electronic Frontier Foundation (EFF).
Last updated April 21, 2014. NOTE: This FAQ is for informational purposes only and does not constitute legal advice. Our aim is to provide a general description of the legal issues surrounding Tor in the United States. Different factual situations and different legal jurisdictions will result in different answers to a number of questions. Therefore, please do not act on this information alone; if you have any specific legal problems, issues, or questions, seek a complete review of your situation with a lawyer licensed to practice in your jurisdiction. Also, if you received this document from anywhere besides the EFF web site or it may be out of date. Got a DMCA notice?