

Hosting your own git repo with Gitolite : Anders M. Andersen. April 4, 2012 After using CVS (A.K.A. “Crappy Versions System”) for way to long we decided to enter the twentieth century and move our code to Git. We had used private Github repos for some smaller projects, but were reluctant to move the whole organizations code to Github, so we started to look for alternatives. We have a lot of consultants, partners and short term employees working with our code so we needed a good way of controlling access to the repos and preferrably without giving each of them a unix user on the server where the repo is hosted. And guess what, Gitolite gives us all that. Git/gitolite: moving repos after setting up gitolite. Moving existing local GIT repository into a fresh gitolite setup. One of the tools I use is gitolite, a nice solution for hosting GIT repositories with privileges control and many more.

Installation is trivial, just follow the tutorial instructions. Let’s say you already have local repository and start to use gitolite on a remote server. This may happen when changing servers, git hosting provider etc. Moving pre-existing repos into gitolite. Master TOC | chapter TOC | support | license WARNING: This is not the latest gitolite; please see the README moving pre-existing repos into gitolite It's best to split this into different use cases.

Case 1 -- few repos: This is for moving one or two repos at a time, when you have a copy of the repo on your workstation. It is also the only way if you have push rights to the admin repo but no shell privileges on the server. Adding and removing repos. Version control - Set up git to pull and push all branches. Pushing new repository to gitolite server. Git Repository Server using Gitolite - kris.me.uk. Some time ago, I covered setting up a git repository server using gitosis.

Since then, gitolite has entered the arena and has built on gitosis adding features such as branch level access control, gitweb control and improved configuration. This guide covers installing gitolite using the non-root method and simple administration. The documentation for gitolite is pretty comprehensive and I encourage you to read the official install and admin instructions. Git push - Pushing existing git repository to gitolite. Configuring gitolite's advanced features. This is the documentation for the contents of the "rc" file ($HOME/.gitolite.rc) on the server.

Until now this documentation was inline, within the rc file itself, but it has grown too large, too unwieldy, and too difficult to grok for people new to gitolite. The documentation follows approximately the same order as the sample variables in the (now reorganised) example "rc" file. [Note: in perl, there is no actual boolean. The undefined value, the number '0', and the empty string, are all 'false'.
Everything else is 'true'. The first section does not need too much elaboration. This section describes variables that, if not carefully used, can cause security issues. Using non-default value for these variables voids the security reward in the README. $GL_ALL_READ_ALL, boolean, default undef Eliminates the access control check for read access. Let's say you want to disallow the archive feature, you would need to change this constant. Git - Gitolite permissions on branches. Gitolite. Note: the latest copy of this section of the ProGit book is always available within the gitolite documentation.

The author would also like to humbly state that, while this section is accurate, and can (and often has) been used to install gitolite without reading any other documentation, it is of necessity not complete, and cannot completely replace the enormous amount of documentation that gitolite comes with. Git has started to become very popular in corporate environments, which tend to have some additional requirements in terms of access control. Gitolite was originally created to help with those requirements, but it turns out that it's equally useful in the open source world: the Fedora Project controls access to their package management repositories (over 10,000 of them!) Access rules. Master TOC | main page | single-page | license | New: Gitolite Essentials book This is for gitolite "g3"; for older (v2.x) documentation click here NOTE: In the following description, "user" means "user or a group that he/she is a member of", and "repo" means "repo, or a group that it is a member of, or a (wild repo) pattern that matches it, or a group that contains a pattern that matches it". what do rules look like Here's an example ruleset.
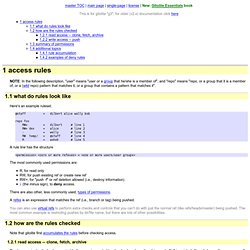
@staff = dilbert alice wally bob repo foo RW+ = dilbert # line 1 RW+ dev = alice # line 2 - = wally # line 3 RW temp/ = @staff # line 4 R = ashok # line 5 A rule line has the structure <permission><zero or more refexes> = <one or more users/user groups> The most commonly used permissions are: R, for read onlyRW, for push existing ref or create new refRW+, for "push -f" or ref deletion allowed (i.e., destroy information)- (the minus sign), to deny access. There are also other, less commonly used, types of permissions. how are the rules checked. Adding and removing repos. Gitolite. This section serves as a quick introduction to Gitolite, and provides basic installation and setup instructions.

It cannot, however, replace the enormous amount of documentation that Gitolite comes with. There may also be occasional changes to this section itself, so you may also want to look at the latest version here.