

Addressing the Challenges Cybercrime-as-a-Service Serves Up. Bienvenue sur My Kaspersky ! Discover Server Health and Hacking Attempts in Web Server error_log Files. In this third and final edition in my series on web server logs, I'll explain what an error_log is and the important information you can find within.

My previous two Nuggets explaining your web server's access_log can be found here and here. In those previous two Nuggets I showed examples of the information that is recorded in your access_log file every time someone visits your website. All of that information is useful for helping you determine how to improve your site. On the other hand, the error_log file is where server problems are saved.
These problems include misconfigurations, missing files, hacking attempts, server errors, and denial of service (DOS) attacks. The error_log file is usually saved in the same directory on your web server as your access_log file. The CERT Division. SANS Information Security Training. Insecure.Org - Nmap Free Security Scanner, Tools & Hacking resources.
Enterprise Cloud Data Protection. Mobile Device Management - Award Winning MDM Solution - MaaS360. Trust, company culture and BYOD security. January 20, 2015 Trust, company culture and BYOD security In a recent survey of senior security decision makers 38 percent cited device security as one of the top worries they have when it comes to mobile device use.

For such organisations BYOD can be a daunting prospect. The idea of allowing employees to use their personal devices at work is still revolutionary for many, and as with any revolutionary idea, it will take some time to become accepted fully. The issue is that all too often devices, and device security, are being used as a scapegoat for regressive and counterproductive IT policies. Organisations therefore have a clear choice: address the security challenge of BYOD and enjoy the benefits; or keep delaying until such a time as it may become too late. For businesses that choose the former, the key to success lies in worrying less about the device.
Top Ten Steps for Apache Webserver Hardening. Introduction This Howto describes the most typical webserver hardening steps to improve security.
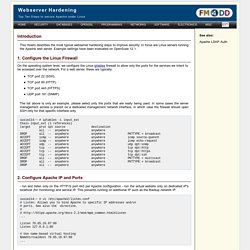
In focus are Linux servers running the Apache web server. Example settings have been evaluated on OpenSuse 12.1. 1. Configure the Linux Firewall On the operating system level, we configure the Linux iptables firewall to allow only the ports for the services we intent to be accessed over the network. The list above is only an example, please select only the ports that are really being used. 2. . - run and listen only on the HTTP/S port 443 per Apache configuration - run the actual website only on dedicated IP's localhost (for monitoring) and service IP. Discover Server Health and Hacking Attempts in Web Server error_log Files. Untitled. Fireeye-poison-ivy-report.pdf. Poison Ivy RAT becoming the AK-47 of cyber-espionage attacks. The Poison Ivy Remote Access Tool (RAT) - often considered a tool for novice "script kiddies" - has become a ubiquitous feature of cyber-espionage campaigns, according to experts.
Research by malware protection firm FireEye has revealed that the tool served as lynchpin of many sophisticated cyber attacks, including the compromise of RSA SecurID data in 2011 and the "Nitro" assault against chemical makers, government offices, defence firms and human-rights groups last year. How to hack a bank (theoretically) One service that some security consultancies provide is called 'red teaming'.

This simply means trying to infiltrate a client's IT systems through any means possible, in order to highlight security vulnerabilities they may not have identified. UK security firm Context Information Security has been commissioned by a number of major financial institutions to attack their systems. Last week, it presented some of the techniques it has used successfully - and how the targets could have thwarted them. The general plan of attack for infiltrating a bank's IT systems is to mimic the so-called 'advanced persistent threat', understood to be the Chinese army's preferred method of cyber attack. This means using a previously undiscovered or 'zero day' software vulnerability to create targeted malware; using social engineering to inject that malware into an organisation's IT infrastructure; using that malware to gain remote access to the company's network; and finally extracting the desired information.
University of Oxford Single Sign-On Login. Setting Up a Pentest Lab with pfSense in VirtualBox. Introduction Penetration testing requirements often force penetration testers to do both external as well as internal assessments.

Daniel Miessler : Technology. Malware - How do I safely inspect a suspicious email attachment? I received a pretty blatantly spammy email to my Gmail account.

I'm not really sure how it made it through the spam filters, since it has all of the telltale signs. The FROM field is spoofed as upsservices@ups.com, but the headers reveal the sender's IP as 178.90.188.166... which points back to an ISP in Kazakhstan. Anyway, attached to the email is a supposed HTML file. Phishing emails and bogus contact: HM Revenue and Customs examples. Network Security Trumps Server Security in the Enterprise. There is a historical conundrum in cybersecurity about where to concentrate security skills, controls, and oversight.

Hackers penetrate networks in order to compromise hosts and steal data. Given this obvious workflow, should CISOs focus security resources on networks, hosts, or a balanced combination of both? ESG recently posed this question to 395 security professionals working at midmarket (i.e., 100 to 999 employees) and enterprise (i.e., more than 1,000 employees) organizations. The results are extremely interesting: Somewhat surprisingly, there is a clear imbalance in most cases. The ESG data also indicates that this behavior is changing. There are several market implications here: Network security vendors remain in the cat-bird seat.
Information Security for the Admin Team - Google Slides.
Governance Policy & Theory. Cloud security. Malware. Tools. Hacking / Pen testing.