

Install tshark On CentOS Linux Using The Yum Package Manager - Question Defense. I use tshark sometimes to strip down packet captures based on specific variables and needed to install tshark on a CentOS Linux server I recently built for various development tasks.
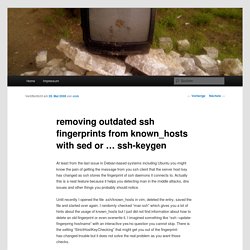
The problem is that when attempting to install tshark using yum it returned an error because there was no package named tshark available in any of the yum repositories I had configured. Error Attempting To Install tshark Using Yum: [root@dev ~]# yum list *TSHARK* Loaded plugins: fastestmirror Loading mirror speeds from cached hostfile * addons: mirror.cogentco.com * base: mirrors.serveraxis.net * epel: ftp.osuosl.org * extras: mirrors.serveraxis.net * rpmforge: apt.sw.be * updates: hpc.arc.georgetown.edu Error: No matching Packages to list As you can see above when attempting to locate any packages containing tshark yum returned an error because there were no packages available that contained the word tshark. Use Yum To Search For The Package That Installs Tshark: SSH Tutorial for Linux - Support Documentation. This document covers the SSH client on the Linux Operating System and other OSes that use OpenSSH.

If you use Windows, please read the document SSH Tutorial for Windows If you use Mac OS X or other Unix based system, you should already have OpenSSH installed and can use this document as a reference. This article is one of the top tutorials covering SSH on the Internet. It was originally written back in 1999 and was completely revised in 2006 to include new and more accurate information. OpenSSH/Client Configuration Files. Client configuration files can be per user or system wide, with the former taking precedence over the latter and run-time arguments in the shell overriding both.

In these configuration files, one parameter per line is allowed with the parameter name followed by its value or values. Empty lines and lines starting with the hash (#) are ignored. An equal sign (=) can be used instead of whitespace between the parameter name and the values. "Add correct host key in known_hosts" / multiple ssh host keys per hostname? How to properly remove an old ssh key. Removing outdated ssh fingerprints from known_hosts with sed or … ssh-keygen. At least from the last issue in Debian-based systems including Ubuntu you might know the pain of getting the message from you ssh client that the server host key has changed as ssh stores the fingerprint of ssh daemons it connects to.
Actually this is a neat feature because it helps you detecting man in the middle attacks, dns issues and other things you probably should notice. Location of Known_hosts file? Editing known_hosts in ubuntu - Ars Technica OpenForum. I foolishly asked this question in the ubuntu forums, instead of going first to the hive and got little useful in response.
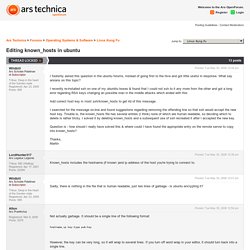
What say arsians on this topic? I recently re-installed ssh on one of my ubunbtu boxes & found that I could not ssh to it any more from the other and got a long error regarding RSA keys changing an possible man in the middle attacks which ended with this: How To Fix Offending key in ~/.ssh/known_hosts file. By Ramesh Natarajan on April 30, 2010 As we discussed earlier in our basic ssh client commands article, when you do ssh to a machine for the 1st time (or whenever there is a key change in the remote machine), you will be prompted to say ‘yes’ for authenticity of host.

This feature is controlled using StrictHostKeyChecking ssh parameter. By default StrictHostKeyChecking is set to yes. The default setting of “StrictHostKeyChecking yes” is the best option from security point of view to protect your system against any trojan horse attacks. Ssh - Remove key from known_hosts. Is it possible to remove a particular host key from SSH's known_hosts file? Install Htop - Linux Process Monitoring for RHEL, CentOS & Fedora.
In our earlier series of system monitoring article where we explained about Iotop (Monitor Linux Disk I/O) tool, now today we are so exciting to install another system process monitoring tool called Htop on our CentOS 6.3 box to see how it works.

It should work on RedHat/Fedora as well. I had heard that htop is replacement of Unix/Linux Top command. I have installed it one of our box and became fond of it. You too can try it out and share your experience with us through comment. Start installing htop and play with it. How Do I Find The Largest Top 10 Files and Directories On a Linux / UNIX / BSD? How To Add Swap on Ubuntu 12.04. About Linux Swapping Linux RAM is composed of chunks of memory called pages.
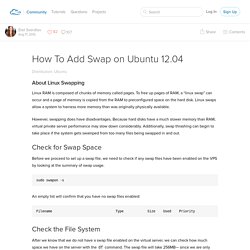
To free up pages of RAM, a “linux swap” can occur and a page of memory is copied from the RAM to preconfigured space on the hard disk. Linux swaps allow a system to harness more memory than was originally physically available. However, swapping does have disadvantages. Because hard disks have a much slower memory than RAM, virtual private server performance may slow down considerably. Check for Swap Space Before we proceed to set up a swap file, we need to check if any swap files have been enabled on the VPS by looking at the summary of swap usage. Bash - What is the Linux equivalent to DOS pause? Linux Command Line Cheat Sheet Free Tips and Tricks Guide. Command line - Terminal output scrolling is gone (Headless 11.10 Server, Upgraded from 10.10) Commands / tmux. Code / Bash / One Liners. [Chapter 35] 35.10 Splitting Files by Context: csplit. Let's look at search patterns first.
![[Chapter 35] 35.10 Splitting Files by Context: csplit](http://cdn.pearltrees.com/s/pic/th/chapter-splitting-context-99703249)
Suppose you have an outline consisting of three main sections. You could create a separate file for each section by typing: % csplit outline /I./ /II./ /III./ 28 number of characters in each file 415 . 372 . 554 . % ls outline xx00 outline title, etc. xx01 Section I xx02 Section II xx03 Section III This command creates four new files (outline remains intact). csplit displays the character counts for each file. Note that the first file (xx00) contains any text up to but not including the first pattern, and that xx01 contains the first section, as you'd expect. If you don't want to save the text that occurs before a specified pattern, use a percent sign as the pattern delimiter:
"Bash" Software Bug May Pose Bigger Threat Than "Heartbleed" - Security. Linux and Unix tr command help and examples. About tr tr syntax tr examples Related commands Linux and Unix main page About tr The tr command automatically translates (substitutes, or maps) one set of characters to another.
Description The tr utility copies the standard input to the standard output with substitution or deletion of selected characters. tr syntax. Awk - A Tutorial and Introduction - by Bruce Barnett. Your browser does not have Javascript enabled. I use Javascript for analytics, and to show ads which pay for the maintenance Last modified: Thu Apr 23 16:37:47 EDT 2015 Part of the Unix tutorials And then there's My blog Table of Contents.
Sed - An Introduction and Tutorial. Last modified: Mon Dec 2 16:50:13 2019 Table of Contents Note - You can click on the table of contents sections to jump to that section. Then click on the section header of any section to jump back to the table of contents. Copyright 1994, 1995 Bruce Barnett and General Electric Company. The Ubuntu Incident. We know that “source” is a bash shell built-in command that executes the content of the file passed as argument in the current shell. BashFAQ. These are answers to frequently asked questions on channel #bash on the freenode IRC network. These answers are contributed by the regular members of the channel (originally heiner, and then others including greycat and r00t), and by users like you.
If you find something inaccurate or simply misspelled, please feel free to correct it! All the information here is presented without any warranty or guarantee of accuracy. Use it at your own risk. When in doubt, please consult the man pages or the GNU info pages as the authoritative references. BASH is a BourneShell compatible shell, which adds many new features to its ancestor.
This FAQ assumes a certain level of familiarity with basic shell script syntax. How do I trim lines read from standard input on bash? Bash - shell replace cr\lf by comma. Sorting - using Linux cut, sort and uniq. Egrep mini-tutorial. Egrep is an acronym for "Extended Global Regular Expressions Print". BashFAQ/011. BashFAQ/011.