

Exploits Database by Offensive Security. Google hacking. Basics[edit] The following search query will locate all websites that have the words "admbook" and "version" in the title of the website.
It also checks to ensure that the web page being accessed is a PHP file. intitle:admbook intitle:version filetype:php One can even retrieve the username and password list from Microsoft FrontPage servers by inputting the given microscript in Google search field: "#-Frontpage-" inurl:administrators.pwd Devices connected to the Internet can be found. Another useful search is following intitle:index.of[1] followed by whatever you want to search. Advanced operators[edit] There are many similar advanced operators which can be use to exploit insecure websites: See also[edit] Operators and more search help - Web Search Help.
You can use symbols or words in your search to make your search results more precise.
Google Search usually ignores punctuation that isn’t part of a search operator. Don’t put spaces between the symbol or word and your search term. A search for site:nytimes.com will work, but site: nytimes.com won’t. Search social media Put @ in front of a word to search social media. Search for a price Put $ in front of a number. Search hashtags Put # in front of a word. Exclude words from your search Put - in front of a word you want to leave out. How to use Google for Hacking. Google serves almost 80 percent of all search queries on the Internet, proving itself as the most popular search engine.

However Google makes it possible to reach not only the publicly available information resources, but also gives access to some of the most confidential information that should never have been revealed. In this post I will show how to use Google for exploiting security vulnerabilities within websites. The following are some of the hacks that can be accomplished using Google. 1. Hacking Security Cameras There exists many security cameras used for monitoring places like parking lots, college campus, road traffic etc. which can be hacked using Google so that you can view the images captured by those cameras in real time. Inurl:”viewerframe? Click on any of the search results (Top 5 recommended) and you will gain access to the live camera which has full controls. you now have access to the Live cameras which work in real-time.
Intitle:”Live View / – AXIS” Google hacking master list. This master list of Google Hacking command sets has show up on a forum in Russia, as well as on Scribd.
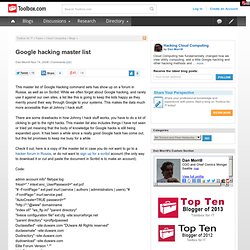
While we often forget about Google hacking, and rarely use it against our own sites, a list like this is going to keep the kids happy as they merrily pound their way through Google to your systems. This makes the data much more accessible than at Johnny I hack stuff. There are some drawbacks in how Johnny I hack stuff works, you have to do a lot of clicking to get to the right hacks.
This master list also includes things I have not seen or tried yet meaning that the body of knowledge for Google hacks is still being expanded upon. It has been a while since a really good Google hack has come out, but this list promises to keep me busy for a while. Code: admin account info" filetype:log ! Nurl:/admin/login.asp inurl:/cgi-bin/sqwebmail? Google Dorks. Cache: If you include other words in the query, Google will highlight those words within the cached document.

For instance, [cache:www.google.com web] will show the cached content with the word “web” highlighted. This functionality is also accessible by clicking on the “Cached” link on Google’s main results page. The query [cache:] will show the version of the web page that Google has in its cache. For instance, [cache:www.google.com] will show Google’s cache of the Google homepage. Link: The query [link:] will list webpages that have links to the specified webpage. Related: The query [related:] will list web pages that are “similar” to a specified web page.