

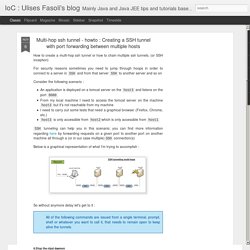
Chaining ssh tunnels. Imagine you're working within a private home network and need to connect to an Oracle database within a corporate network accessible only through a bastion host hidden within the corporate network.

Odd as that sounds, it's a typical network configuration, as follows: The layout is very simple, when you're within the corporate network you must use the bastion host to access the vault (e.g., the Oracle database). The arrows in the above diagram represent the directionality of the various firewall rules, and in this case, these are SSH-only. A workstation within the corporate network would simply create an SSH-tunnel through the bastion to the vault.
Technically, there's a line of (completely separate) SSH connections from the private home network all the way to the vault, but there is absolutely no way for either side to talk directly. Each line could represent an SSH-tunnel, in which case, if we chain these tunnels together, then we could connect to the vault from the home network. Step 1. X over SSH - A Tutorial. Note: I was able to use FreeBSD on RAT's hardware to test some of the X over SSH scenarios.
LAPTOP to BSD-RAT worked fine. 1. On RAT (where the X Client programs are located), you can be in runlevel 3 or runlevel 5. It does not matter. 2. How to Install and Configure VNC on Ubuntu 14.04. Introduction VNC, or "Virtual Network Computing", is a connection system that allows you to use your keyboard and mouse to interact with a graphical desktop environment on a remote server.

VNC makes managing files, software, and settings on a remote server easier for users who are not yet comfortable with working with the command line. In this guide, we will be setting up VNC on an Ubuntu 14.04 server and connecting to it securely through an SSH tunnel. The VNC server we will be using is TightVNC, a fast and lightweight remote control package. This choice will ensure that our VNC connection will be smooth and stable even on slower Internet connections.
Prerequisites Before you begin with this guide, there are a few steps that need to be completed first. Initial Server Setup with Ubuntu 14.04. Introduction When you first create a new Ubuntu 14.04 server, there are a few configuration steps that you should take early on as part of the basic setup.
This will increase the security and usability of your server and will give you a solid foundation for subsequent actions. Step One — Root Login To log into your server, you will need to know your server's public IP address and the password for the "root" user's account. If you have not already logged into your server, you may want to follow the first tutorial in this series, How to Connect to Your Droplet with SSH, which covers this process in detail. If you are not already connected to your server, go ahead and log in as the root user using the following command (substitute the highlighted word with your server's public IP address): ssh root@SERVER_IP_ADDRESS Complete the login process by accepting the warning about host authenticity, if it appears, then providing your root authentication (password or private key).
About Root adduser demo. X11 Forwarding using SSH. As I have explained earlier, using XDMCP to display X across Internet is basically a no-no, due to it's lack of encryption across the Internet.
One way to enforce the traffic security is to use the SSH by the way of X11 tunnelling or port forwarding. SSH (Secure Shell) is developed in 1995 by Tatu Ylonen to replace the insecure telnet, ftp, scp, rcp, rlogin, rsh, etc. The first thing you need to know is that X11 forwarding using SSH is different from your regular, non-secure way of running X Window. To start this setup, you need an additional piece of information.
First, you must have your SSH package installed. Open up the command putty.exe by double-click it. Xorg - Run X clients over multi-hop ssh tunnel. How to tunnel X over SSH using Port Forwarding : JuiceSSH Helpdesk. Modified on: Sat, 20 Dec, 2014 at 2:44 PM This port forwarding configuration describes how to tunnel X over SSH.
It uses X Server (available on Play Store) to forward remote X applications from the SSH server. Please adjust addresses and ports to suit your needs. Requirements A Pro license for JuiceSSH, enabling Port Forwarding functionality.An X Server on your Android device which is listening on port 6000.An SSH server named ssh.myxdomain.com which is listening on port 22. Instructions For more in-depth study about X servers and X clients, refer to documentation on site. Was this answer helpful? Send feedback Sorry we couldn't be helpful. LiNUX Horizon - SSH Port Forwarding (SSH Tunneling) Sintax: ssh -L localport:host:hostport user@ssh_server -N where: -L - port forwarding parameters (see below) localport - local port (chose a port that is not in use by other service) host - server that has the port (hostport) that you want to forward hostport - remote port -N - do not execute a remote command, (you will not have the shell, see below) user - user that have ssh access to the ssh server (computer) ssh_server - the ssh server that will be used for forwarding/tunneling Without the -N option you will have not only the forwardig port but also the remote shell.

Try with and without it to see the difference. Note: 1. Privileged ports (localport lower then 1024) can only be forwarded by root. 2. IoC : Ulises Fasoli's blog: Multi-hop ssh tunnel - howto : Creating a SSH tunnel with port forwarding between multiple hosts. FontIcons have become really popular in the past few years and they have a lot of advantages such as : They are vector based so no loss in quality when re-sizing The ability to easily change their size/color/shade ; without involving an image editor (they are just fonts!)
The ability to combine font-icons or add text-decorations, gradients, textures (depending on browser support) When creating FontIcons you have a few options, here I will discuss how to create them from PNG files 1. SSH Tunnel - Local and Remote Port Forwarding Explained With Examples - Trackets Blog. There are two ways to create an SSH tunnel, local and remote port forwarding (there’s also dynamic forwarding, but we won’t cover that here).

The best way to understand these is by an example, let’s start with local port forwarding. Imagine you’re on a private network which doesn’t allow connections to a specific server. Let’s say you’re at work and imgur.com is being blocked.