

Chromium found to be downloading a binary blob on first run. Mitterer even questioned whether Google should be trusted as an upstream contributor to the Debian project following the incident, especially given that the online ad giant's known cooperation with US government data snooping, voluntary and otherwise.

Mitterer is right. They shouldn't be. Updated: Time to disconnect the microphone? Chrome and the open source variant Chromium were downloading audio listening software without permission, not in the extensions list, and with audio set to 'enable'.

When it comes to sex and surveillance, if it's possible, then someone somewhere will try it, so when researchers reported this month that Google had secretly installed software on PCs enabling listening to conversations in the room and export of the audio without any permission being granted, concerns remained after the ‘bug fix'. Open source developers found that Google's Chrome downloaded software to support its “OK, Google” hotword detection – including in the open source version Chromium browser – but complained that it did not appear in the extension list. Initially, they claimed it activated audio without user permission.
Chromium downloads a binary blob which listens to computers mic automatically without users consent. : privacy. Google Chrome Listening In To Your Room Shows The Importance Of Privacy Defense In Depth. Yesterday, news broke that Google has been stealth downloading audio listeners onto every computer that runs Chrome, and transmits audio data back to Google.

Effectively, this means that Google had taken itself the right to listen to every conversation in every room that runs Chrome somewhere, without any kind of consent from the people eavesdropped on. In official statements, Google shrugged off the practice with what amounts to “we can do that”. It looked like just another bug report. "When I start Chromium, it downloads something. " Followed by strange status information that notably included the lines "Microphone: Yes" and "Audio Capture Allowed: Yes". Without consent, Google’s code had downloaded a black box of code that – according to itself – had turned on the microphone and was actively listening to your room.
A brief explanation of the Open-source / Free-software philosophy is needed here. Obviously, your own computer isn’t the one to analyze the actual search command. Chromium suddenly starts downloading a binary blob. By Jake EdgeJune 17, 2015 A Debian bug that was filed at the end of May serves as a reminder that even open-source software is not immune to some of the problems of proprietary software.
In this case, Chromium 43 was silently downloading a browser extension to enable the "OK Google" voice activation "feature" of the browser, which is somewhat reminiscent of the various sideloading schemes that plague downloads of "free" software, particularly on Windows. The download was a binary blob, of course, so its contents cannot be vetted in any real sense. As might be guessed, Debian developers were not amused, but it should also serve as a bit of a wakeup call to all of the free-software world.
The extension in question is called "Chrome Hotword" and the download is a native client (NaCl) shared module that includes executable content. To summarize, a popular open-source web browser does a surreptitious download of a program and hides the download and the existence of the program from the user. #786909 - chromium: unconditionally downloads binary blob. Reply or subscribe to this bug.
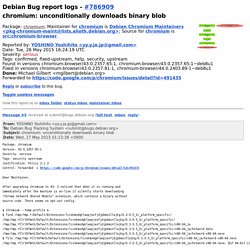
Report forwarded to debian-bugs-dist@lists.debian.org, team@security.debian.org, secure-testing-team@lists.alioth.debian.org, Debian Chromium Maintainers <pkg-chromium-maint@lists.alioth.debian.org>:Bug#786909; Package chromium. (Tue, 26 May 2015 16:24:24 GMT) Full text and rfc822 format available. Acknowledgement sent to YOSHINO Yoshihito <yy.y.ja.jp@gmail.com>: New Bug report received and forwarded. Chromium unconditionally downloads binary blob. > without any evidence to support it this is like calling someone a murderer because he went to the same high school as a murderer.

That's a pretty flawed analogy. If you're going to examine it from a criminal act point of view, let's really look at it that way. If installing a rootkit is equivalent to premeditated murder, then the murderer must have motive, means, and opportunity. Let's take Sony as a good example of a company guilty of installing a rootkit. Motive: Prevent unauthorized copying of their music CDs. Now, let's look at what we know about this Chromium binary blob silent install (note I'm not calling it a rootkit, as I agree with you that's taking it a bit far, but it would theoretically be possible to install one via the same method). Issue 500922 - chromium - Hotword behaviour in chromium v43 (binary blob download) - An open-source project to help move the web forward.