

Squel.js - SQL query string builder for Javascript. Squel.js - lightweight Javascript library for building SQL query strings. - usable with node.js and in the browser. - well tested (~ 340 Mocha tests).
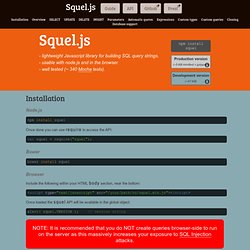
Installation Node.js Once done you can use require to access the API: Bower Browser Include the following within your HTML body section, near the bottom: Once loaded the squel API will be available in the global object: NOTE: It is recommended that you do NOT create queries browser-side to run on the server as this massively increases your exposure to SQL Injection attacks.
Overview Squel helps you quickly and easily build SQL query strings through an object oriented API. It requires less effort - instead of having to use brittle methods like string concatenation and substitution you get a nice clean API to do the hard work for you. Ok, now you're convinced! Squel uses method chaining to make things easy. Hint: You can run the example above by clicking it! You can simply write: Note: All of Squel's builders provide the toString() method. Fields Joins. MySQL. MySQL (/maɪ ˌɛskjuːˈɛl/ "My S-Q-L",[6] officially, but also called /maɪ ˈsiːkwəl/ "My Sequel") is (as of March 2014[update]) the world's second most[nb 1] widely used[9][10] open-source relational database management system (RDBMS).[11] It is named after co-founder Michael Widenius's daughter, My.[12] The SQL phrase stands for Structured Query Language.[6] The MySQL development project has made its source code available under the terms of the GNU General Public License, as well as under a variety of proprietary agreements.

MySQL was owned and sponsored by a single for-profit firm, the Swedish company MySQL AB, now owned by Oracle Corporation.[13] For commercial use, several paid editions are available, and offer additional functionality. Applications which use MySQL databases include: TYPO3, MODx, Joomla, WordPress, phpBB, MyBB, Drupal and other software. Interfaces[edit] Graphical[edit] SQL Injection Attacks by Example. A customer asked that we check out his intranet site, which was used by the company's employees and customers.

This was part of a larger security review, and though we'd not actually used SQL injection to penetrate a network before, we were pretty familiar with the general concepts. We were completely successful in this engagement, and wanted to recount the steps taken as an illustration. "SQL Injection" is subset of the an unverified/unsanitized user input vulnerability ("buffer overflows" are a different subset), and the idea is to convince the application to run SQL code that was not intended.
If the application is creating SQL strings naively on the fly and then running them, it's straightforward to create some real surprises. We'll note that this was a somewhat winding road with more than one wrong turn, and others with more experience will certainly have different -- and better -- approaches. We speculate that the underlying SQL code looks something like this: A standalone query of. Xp_cmdshell. Executes a given command string as an operating-system command shell and returns any output as rows of text.

Grants nonadministrative users permissions to execute xp_cmdshell. Note When executing xp_cmdshell with the Microsoft® Windows® 98 operating systems, the return code from xp_cmdshell will not be set to the process exit code of the invoked executable. The return code will always be 0. Syntax xp_cmdshell {'command_string'} [, no_output] Arguments 'command_string' Is the command string to execute at the operating-system command shell. command_string is varchar(8000) or nvarchar(4000), with no default. command_string cannot contain more than one set of double quotation marks. No_output Is an optional parameter executing the given command_string, and does not return any output to the client. SQL Injection Attacks by Example.
A customer asked that we check out his intranet site, which was used by the company's employees and customers.

This was part of a larger security review, and though we'd not actually used SQL injection to penetrate a network before, we were pretty familiar with the general concepts. We were completely successful in this engagement, and wanted to recount the steps taken as an illustration. "SQL Injection" is subset of the an unverified/unsanitized user input vulnerability ("buffer overflows" are a different subset), and the idea is to convince the application to run SQL code that was not intended.
If the application is creating SQL strings naively on the fly and then running them, it's straightforward to create some real surprises. We'll note that this was a somewhat winding road with more than one wrong turn, and others with more experience will certainly have different -- and better -- approaches. We speculate that the underlying SQL code looks something like this: A standalone query of. SQL INJECTION (ERROR BASED) Timeline. PHPeasystep - Learn PHP and MySQL.