

Practical Padding Oracle Attacks on RSA. We introduce RSA giving some simple tools to “play” with it.
The only thing we need to recall of RSA is that encryption E(m) and decryption D(y) are defined as exponentiation modulo a big n (at least 1024 bits), respectively using the public e and the private d exponent. Encryption and decryption are such that such that D(E(m)) = m. The OpenSSL toolkit provides very flexible command line tools to perform cryptographic operations. XSLT Server Side Injection Attacks. Detection and recovery of NSA’s covered up tracks. Part of the NSA cyber weapon framework DanderSpritz is eventlogedit, a piece of software capable of removing individual lines from Windows Event Log files.
Now that this tool is leaked and public, any criminal willing to remove its traces on a hacked computer can use it. Fox-IT has looked at the software and found a unique way to detect the use of it and to recover the removed event log entries. Introduction A group known as The Shadow Brokers published a collection of software, which allegedly was part of the cyber weapon arsenal of the NSA. Part of the published software was the exploitation framework FuzzBunch and post-exploitation framework DanderSpritz. OSCP Course & Exam Preparation - Ellingson Mineral. Full disclosure I am not a penetration tester and I failed my OSCP exam twice before eventually passing on the third attempt.
I owned more than 90% of boxes in the labs (including the big three) but when it came to the exam I just kept bombing out. I am hoping something I share here will prevent you from making the same mistakes. Lab Time After years of wanting to do OSCP I got lucky and my employer paid for the full 90 days lab time. This allowed me to put alot of time into the lab network and pwn all but 5 boxes.
How does Ethereum work, anyway? – Preethi Kasireddy. Now that you’ve gotten the 10,000-foot overview of what a blockchain is, let’s dive deeper into the main components that the Ethereum system is comprised of: accountsstategas and feestransactionsblockstransaction executionminingproof of work One note before getting started: whenever I say “hash” of X, I am referring to the KECCAK-256 hash, which Ethereum uses.
Are you aware? Comcast is injecting 400+ lines of ... - Xfinity Help and Support Forums. I just learned of this dispicable Comcast practice today and I am livid.
Comcast began injecting 400+ lines of JavaScript code in to pages I requested on the internet so that when the browser renders the web page, the JavaScript generates a pop up trying to up-sell me a new modem. When you call the number in the popup, they're quick to tell you that you need a new modem, which in my case is not true. Titre. Asintsov: Data exfiltration with Metasploit: meterpreter DNS tunnel. Meterpreter is a well-known Metasploit[1] remote agent for pentester's needs.

This multi-staged payload is a good, flexible and easy-to-use platform that allows pentesters to have remote control over pwnedpenetrated host[2]. Currently it supports following "network" transports:Binding TCP portReverse connection over TCP/IPReverse connection over HTTP. Nnamon/linux-exploitation-course: A Course on Intermediate Level Linux Exploitation. Neat tricks to bypass CSRF-protection. The Infamous Windows “Hello World” Program. Charles Petzold on writing books, reading books, and exercising the internal UTM December 8, 2014New York, N.Y.
A recent blog post by consultant John Cook reminded everybody about the infamous "Hello World" programs in the early chapters of the first five editions of Programming Windows: “Hello world” is the hard part. Reverse engineering the Intel FSP… a primer guide! Recently, I’ve finished reverse engineering the Intel FSP-S “entry” code, that is from the entry point (FspSiliconInit) all the way to the end of the function and all the subfunctions that it calls.

This is only some initial foray into reverse engineering the FSP as a whole, but reverse engineering is something that takes a lot of time and effort. Today’s blog post is here to illustrate that, and to lay the foundations for understanding what I’ve done with the FSP code (in a future blog post). Over the years, many people asked me to teach them what I do, or to explain to them how to reverse engineer assembly code in general.
Sometimes I hear the infamous “How hard can it be?” Catchphrase. Securing an ASP.NET Core Web API 2 using Azure AD B2C – Sara Ford's Blog. Bypassing SAML 2.0 SSO with XML Signature Attacks. We’ve recently noticed a trend with a lot of New Zealand sites wanting to implement Single Sign-On (SSO) to combat the proliferation of passwords, including many government services.
The most prevalent standard for doing this, providing interoperability between many vendors’ frameworks and multiple languages, is SAML 2.0. The usual mechanism for this passes the SAML response certifying the user’s identity through the web browser, using a signature to prevent tampering. Unfortunately, many SAML consumers don’t validate responses properly, allowing attacks up to and including full authentication bypass. When signing in to a site with SAML 2.0, there are three parties involved - the Service Provider (‘SP’, the web application we want to access), the Principal (the user logging in) and the Identity Provider (‘IdP’, the authority). We want to accomplish the aim of getting the Identity Provider to tell the Service Provider, in a trustworthy way, who the Principal is.
HTTP Redirect Binding. KRACK - Casser le WPA2 - hackndo. Image Steganography: Hiding text in images using PHP - The Debuggers. Steganography is the art and science of writing hidden message in such a way that no one, apart from the sender and intended recipient, suspects the existence of the message.
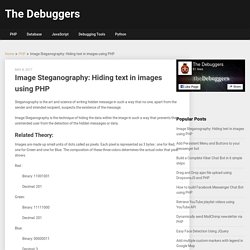
Image Steganography is the technique of hiding the data within the image in such a way that prevents the unintended user from the detection of the hidden messages or data. Related Theory: Images are made up small units of dots called as pixels. Each pixel is represented as 3 bytes : one for Red, one for Green and one for Blue. The composition of these three colors determines the actual color that pixel shows. Understanding Ethereum Smart Contracts - Gjermund Bjaanes. You might have heard the term “smart contract,” and you might even know that they are “code” you can run on a blockchain.
But how can you run code on a blockchain? It’s not the easiest concept to wrap your head around. Advbof. Inject All the Things - Shut Up and Hack. Well, its 2017 and I’m writing about DLL injection. It could be worse. DLL injection is a technique used by legitimate software to add/extend functionality to other programs, debugging, or reverse engineering. It is also commonly used by malware in a multitude of ways. This means that from a security perspective, it’s imperative to know how DLL injection works. I wrote most of the code of this small project, called ‘injectAllTheThings’, a while ago when I started developing custom tools for Red Team engagements (in order to emulate different types of threat actors).
Below is the output of the tool, showing all the options and techniques implemented. Découvrez l'attaque "Return Oriented Programming" ! Reversing DirtyC0W - Life At Tetrane. Everybody keeps in mind the Dirtyc0w Linux kernel bug. For those who don't, take some time to refresh your memory here. The kernel race condition is triggered from user-space and can easily lead a random local user to write into any root owned file. In this article, we will demonstrate how REVEN can help reverse engineering a kernel bug such as Dirtyc0w. Our starting point will be a REVEN scenario recording of an occurence of the bug, together with the corresponding execution trace generated by REVEN. XSLT Server Side Injection Attacks. Reverse Engineering The MacOS AirPlayUIAgent - Part 001 — rotlogix. To be honest with you, I have no real purpose for this blog series.
I plan on writing about my past time efforts to reverse engineer random things I find on my laptop. Maybe I learn something, maybe you learn something, maybe we don't learn anything, maybe we fuck off and join the circus. I've dicked around with a lot AirPlay shit in the past, and found the iOS implementations pretty interesting, so I decided to checkout what was going on locally. Cours n°16. Intro to Analyze NFC Payment Methods & Contactless Cards – Salvador Mendoza Blog. Learn from your attackers - SSH HoneyPot. How does blockchain really work? I built an app to show you. A journey into Radare 2 – Part 2: Exploitation – Megabeets. Prologue Welcome back to the second part of our journey into the guts of radare2!
Shellphish/how2heap: A repository for learning various heap exploitation techniques. Eset gazer. Electrical Engineering and Computer Science. Electrical Engineering and Computer Science. T1106220. Petit Manuel du ROP à l'usage des débutants - Daily Security. De retour ! Après plus d'un an d'absence sur le blog, je décide enfin d'écrire un article annoncé sur Twitter il y a déjà plusieurs mois. Lorsque l'on débute dans le monde des exploits système, on se retrouve facilement bloqué lors de l'apprentissage du Return Oriented Programming (ROP). Dans cet article, je vais vous expliquer une méthode de ROP qui fonctionne la plupart du temps et qui a l'avantage de ne pas utiliser de l'instruction int 0x80 ; ce genre d'instruction étant souvent rare dans un binaire. Les prérequis (fortement recommandés) : Google Cloud Platform Blog: Introducing App Engine firewall, an easy way to control access to your app. Analysing a recent Poison Ivy sample.
Linux Network Commands - DZone DevOps. DOMAngularSandboxEscapes. Restic cryptography. Cisco's Talos Intelligence Group Blog: Booters with Chinese Characteristics: The Rise of Chinese Online DDoS Platforms. DDoS tools and services remain some of the most popular offerings in the Chinese underground market. Android NDK - Reverse engineering d'une application ARM - NES. TR17 ME11 Static. Mining Bitcoin with pencil and paper. b81efa3a4c5826fa441852bd63a402c6. 806. 1708.06733v1. Exploiting JSON Cross Site Request Forgery (CSRF) using Flash. Scan multiple organizations with Shodan and Golang. Bug Bounty example. Guide to Ransomware Prevention & Detection. Exploiting Script Injection Flaws in ReactJS Apps – DailyJS – Medium. How to Embed a Metasploit Payload in an Original .Apk File. Hybrid focused crawling on the Surface and the Dark Web.
CoMisSion – Whitebox CMS analysis – Intrinsec. Build Your Own Linux: Presented by Linux Academy. Technique du Canari : Bypass - hackndo. MJS 053 Weichselbaum CSP. API security testing - tips to prevent getting pwned : Assertible. WHID Injector: an USB-Rubberducky/BadUSB on Steroids: Weaponize a Mouse with WHID Injector for Fun & W00t. Let's Learn: How to Obtain Cerber (CRBR) Ransomware Configuration. Make your own USB Rubber Ducky using a normal USB stick. The Complete Guide To Switching From HTTP To HTTPS. DNS Sinkhole setup. Reverse Engineering an Eclipse Plugin – Learning Security. Intro to Linux Forensics. Dumping the GBA BIOS. Awesome-Fuzzing/README.md at master · secfigo/Awesome-Fuzzing. Griffin asplos17. Hack-with-Github/Awesome-Hacking: A collection of various awesome lists for hackers, pentesters and security researchers.
Hackers-arise. Java Deserialization Exploit Resulting RCE on Thick Client Penetration Testing. How to develop your own Boot Loader - CodeProject. Open Analysis Live: Viewer Submission - Decoding Malicious .vbs Scripts. Open Analysis Live: Reverse Engineering a DGA (Domain Generation Algorithm) How to get a Super Stelfy Shell (that AV doesn't pick up) - Tutorials - 0x00sec - The Home of the Hacker. Mobile Top 10 2016-Top 10. Top 10 2017-Top 10. Exploiting Second Order SQLi Flaws by using Burp & Custom Sqlmap Tamper – Pentest Blog. Reverse Engineering a JavaScript Obfuscated Dropper.
Linux heap exploitation intro series: used and abused – use after free. A Tree-Walk Interpreter · Crafting Interpreters. Firewalls applicatifs : quelques conseils pour bien les utiliser.